What Is Data Security?
June 30, 2021
Data Security Defined
Data security refers to the protective measures employed to secure data against unapproved access and to preserve data confidentiality, integrity, and availability. Data security best practices include data protection techniques such as data encryption, key management, data redaction, data subsetting, and data masking, as well as privileged user access controls and auditing and monitoring.
Data Security Best Practices
Data security best practices should be leveraged both on-premises and in the cloud in order to mitigate the risk of a data breach and to help achieve regulatory compliance. Specific recommendations can vary, but typically call for a layered data security strategy architected to apply a defense-in-depth approach. Different controls mitigate different threat vectors. Distinct solution areas include the abilities to assess, detect and monitor database activity and threats.
The Importance of Data Security
Data is one of the most important assets for any organization. As such, it is paramount to safeguard data from any and all unauthorized access. Data breaches, failed audits, and failure to comply with regulatory requirements can all result in reputational damage, loss of brand equity, compromised intellectual property, and fines for noncompliance. Under the European Union General Data Protection Regulation (GDPR), data breaches can lead to fines of up to 4% of an organization’s global annual revenue, often resulting in significant financial loss. Sensitive data includes personally identifiable information, financial information, health information, and intellectual property. Data must be protected to help avoid a data breach and to help achieve compliance.
Data Security and GDPR
Data masking, data subsetting, and data redaction are techniques for reducing exposure of sensitive data contained within applications. These technologies play a key role in addressing anonymization and pseudonymization requirements associated with regulations such as EU GDPR. The European Union GDPR was built on established and widely accepted privacy principles, such as purpose limitation, lawfulness, transparency, integrity, and confidentiality. It strengthens existing privacy and security requirements, including requirements for notice and consent, technical and operational security measures, and cross-border data flow mechanisms. In order to adapt to the new digital, global, and data-driven economy, the GDPR also formalizes new privacy principles, such as accountability and data minimization.
Under the General Data Protection Regulation (GDPR), data breaches can lead to fines of up to four percent of a company’s global annual turnover or €20 million, whichever is greater. Companies collecting and handling data in the EU will need to consider and manage their data handling practices including the following requirements:
- Data Security. Companies must implement an appropriate level of security, encompassing both technical and organizational security controls, to prevent data loss, information leaks, or other unauthorized data processing operations. The GDPR encourages companies to incorporate encryption, incident management, and network and system integrity, availability, and resilience requirements into their security program.
- Extended rights of individuals. Individuals have a greater control—and ultimately greater ownership of–their own data. They also have an extended set of data protection rights, including the right to data portability and the right to be forgotten.
- Data breach notification. Companies have to inform their regulators and/or the impacted individuals without undue delay after becoming aware that their data has been subject to a data breach.
- Security audits. Companies will be expected to document and maintain records of their security practices, to audit the effectiveness of their security program, and to take corrective measures where appropriate.
What Are the Challenges of Database Security?
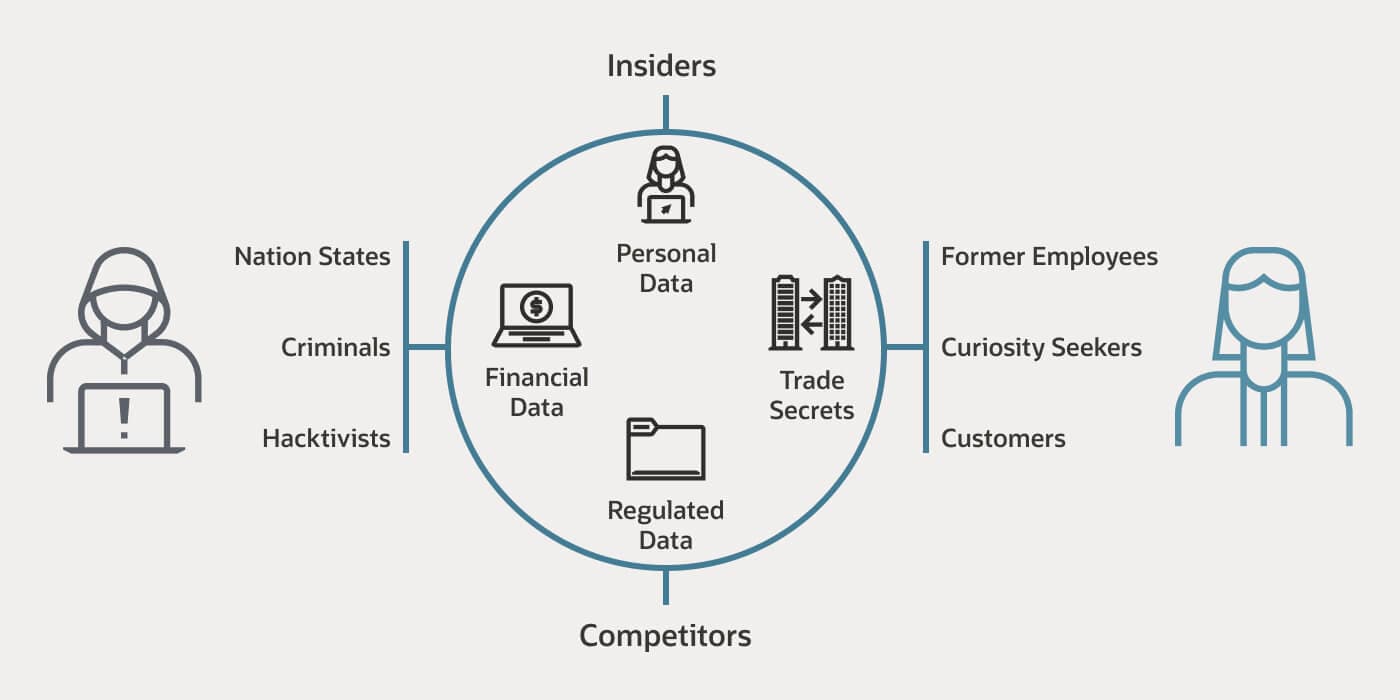
Databases are valuable repositories of sensitive information, which makes them the primary target of data thieves. Typically, data hackers can be divided into two groups: outsiders and insiders. Outsiders include anyone from lone hackers and cybercriminals seeking business disruption or financial gain, or criminal groups and nation state-sponsored organizations seeking to perpetrate fraud to create disruption at a national or global scale. Insiders may comprise current or former employees, curiosity seekers, and customers or partners who take advantage of their position of trust to steal data, or who make a mistake resulting in an unintended security event. Both outsiders and insiders create risk for the security of personal data, financial data, trade secrets, and regulated data.
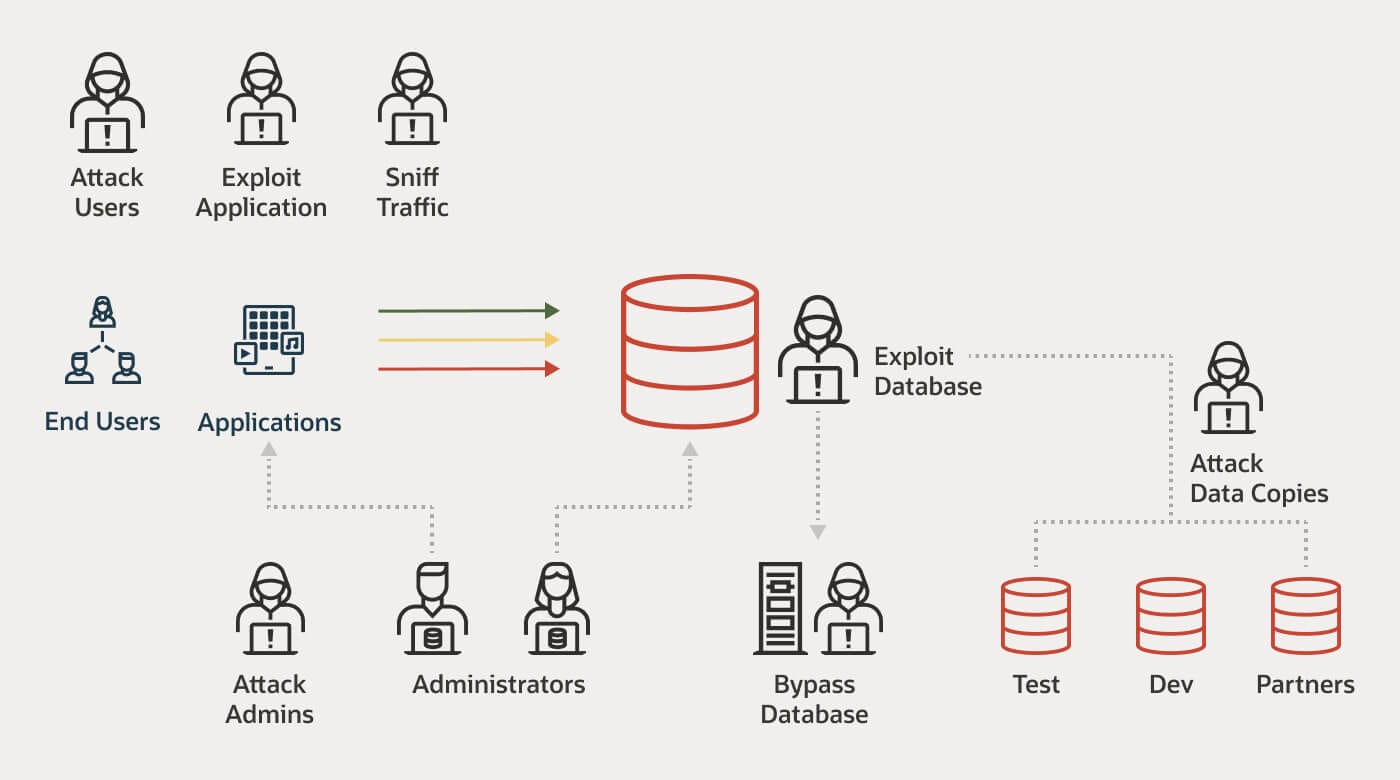
Cybercriminals have a variety of approaches they employ when attempting to steal data from databases:
- Compromising or stealing the credentials of a privileged administrator or application. This is usually through email-based phishing, other forms of social engineering, or by using malware to uncover the credentials and ultimately the data.
- Exploiting weaknesses in applications with techniques such as SQL injection or bypassing application layer security by embedding SQL code into a seemingly innocuous end-user provided input.
- Escalating run-time privileges by exploiting vulnerable applications.
- Accessing database files that are unencrypted on the disk.
- Exploiting unpatched systems or misconfigured databases to bypass access controls.
- Stealing archive tapes and media containing database backups.
- Stealing data from nonproduction environments, such as DevTest, where data may not be as well protected as in production environments.
- Viewing sensitive data through applications that inadvertently expose sensitive data that exceeds what that application or user should be able to access.
- Human error, accidents, password sharing, configuration mistakes, and other irresponsible user behavior, which continue to be the cause of nearly 90% of security breaches.
Database Security Best Practices
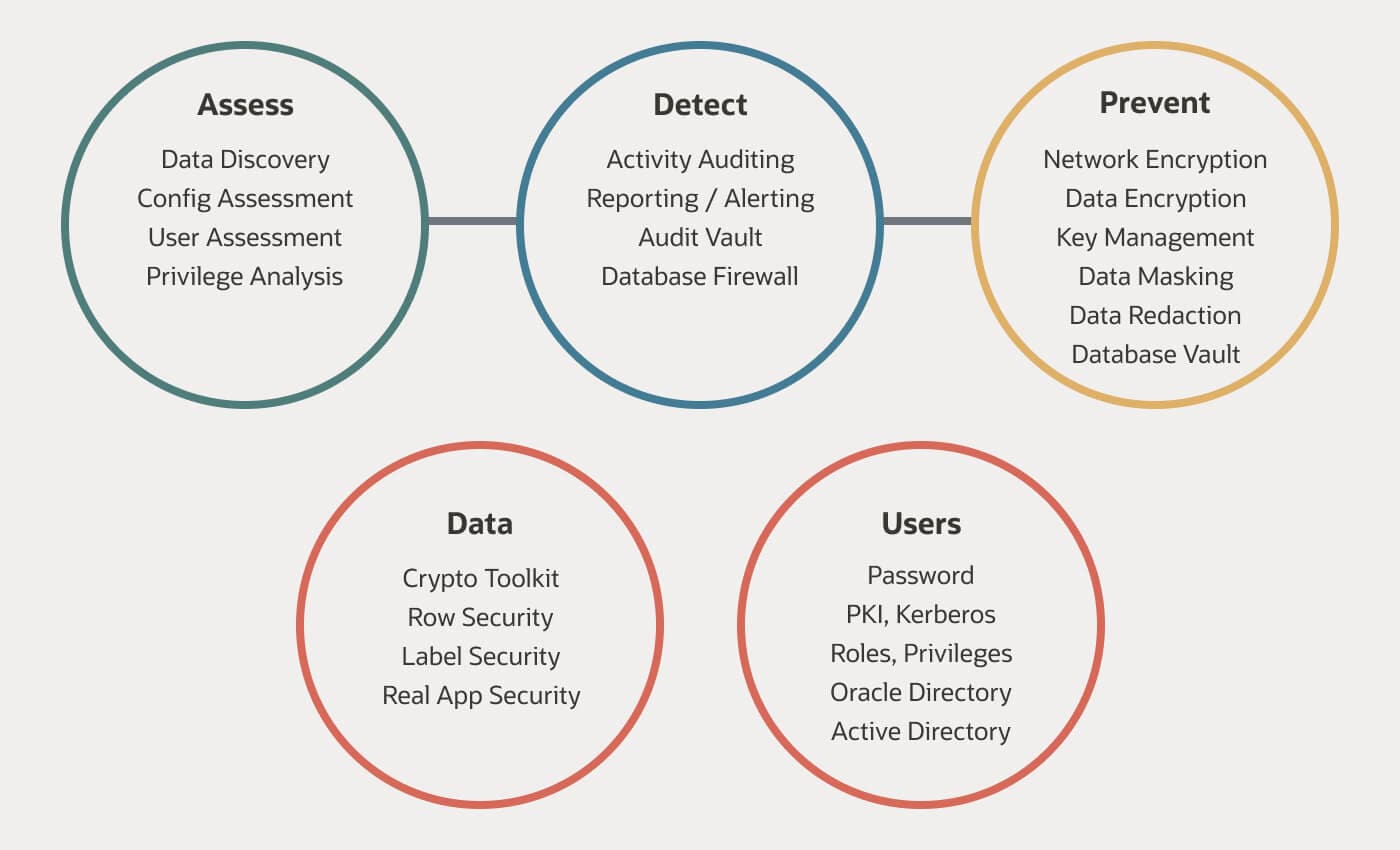
A well-structured database security strategy should include controls to mitigate a variety of threat vectors. The best approach is a built-in framework of security controls that can be deployed easily to apply appropriate levels of security. Here are some of the more commonly used controls for securing databases:
- Assessment controls help to assess the security posture of a database and should also offer the ability to identify configuration changes. Organizations can set a baseline and then identify drift. Assessment controls also help organizations to identify sensitive data in the system, including type of data and where it resides. Assessment controls seek to answer the following questions:
- Is the database system configured properly?
- Are patches up-to-date and applied regularly?
- How are user privileges managed?
- What sensitive data is in the database system? How much? Where does it reside?
- Detective controls monitor user and application access to data, identify anomalous behaviors, detect and block threats, and audit database activity to deliver compliance reporting.
- Preventive controls block unauthorized access to data by encrypting, redacting, masking, and subsetting data, based on the intended use case. The end goal of preventive controls is to halt unauthorized access to data.
- Data-specific controls enforce application-level access policies within the database, providing a consistent authorization model across multiple applications, reporting tools, and database clients.
- User-specific controls enforce proper user authentication and authorization policies, ensuring that only authenticated and authorized users have access to data.
Data Security Solutions
Reduce the risk of a data breach and simplify compliance with data security best practices, including encryption, key management, data masking, privileged user access controls, activity monitoring, and auditing.
- Data protection: Reduce the risk of a data breach and noncompliance with solutions to satisfy a wide range of use cases such as encryption, key management, redaction, and masking. Learn about Data Safe.
- Data access control: A fundamental step in securing a database system is validating the identity of the user who is accessing the database (authentication) and controlling what operations they can perform (authorization). Strong authentication and authorization controls help protect data from attackers. Additionally, enforcing separation of duties helps to prevent privileged users from abusing their system privileges to access sensitive data, and also helps to prevent accidental or malicious changes to the database.
- Auditing and monitoring: All database activity should be recorded for auditing purposes—this includes activity happening over the network, as well as activity triggered within the database (typically through direct login) which bypasses any network monitoring. Auditing should work even if the network is encrypted. Databases must provide robust and comprehensive auditing that includes information about the data, the client from where the request is being made, the details of the operation and the SQL statement itself.
- Securing databases in the cloud: Cloud database deployments can reduce costs, free up staff for more important work, and support a more agile and responsive IT organization. But those benefits can come with additional risk, including an extended network perimeter, expanded threat surface with an unknowable administrative group, and shared infrastructure. However, by employing the proper database security best practices, the cloud can provide better security than most organizations have on-premises, all while reducing costs and improving agility.
