Exploring Networking, Services, and the New Image Packaging System In Oracle Solaris 11
This article is Part 2 of a two-part series that describes how I installed and explored Oracle Solaris 11. It focuses on the new packaging system and the way Oracle Solaris 11 handles networking and services.
Table of Contents
Oracle Solaris 11 Networking
First, let's talk about networking. In Oracle Solaris 11, networking has changed a lot. My immediate concern is not to explain every detail about networking, but I'd like to show you the fundamentals.
To start, there is a good GUI (shown in Figure 1) that can help us configure the Oracle Solaris 11 network. To open the GUI from the desktop, select System -> Administration -> Network:

Figure 1 - GUI for Configuring Oracle Solaris 11 Network
This new network tool shows us that our network has already been configured using DHCP, our IP address is 192.168.105/24, the speed is 1Gb/s, and the network is connected.
Do you remember my requirement in Part 1 for having a DHCP service when you were installing Oracle Solaris 11 from the Live Media DVD? The reason for that is Reactive Network Configuration (RNC), formerly known as NWAM, which automatically configures the network following some rules.
It's possible to set some RNC customization based on a concept named Network Configuration Profiles (NCPs), which makes it possible for the system to connect it to a wired or wireless network, depending on our system's physical/logical location, for example. Nonetheless, all wired and wireless networks are kept in the list shown in Figure 1, and RNC uses an ordered connection process until it successfully connects. By the way, an NCP consists of one or more Network Configuration Units (NCUs), which are containers that store network object configurations, for example, a network interface.
For the Show box in this screen, you can select the Network Profile option. The GUI shows us two network profiles (see Figure 2): Automatic (Reactive Network Configuration) and DefaultFixed (which is outside the control of Reactive Network Configuration). Initially, Oracle Solaris 11 is configured using RNC (through the DHCP service), but we can give up this easy option and instead perform all configuration manually from a terminal window using the dladm and ipadm commands.

Figure 2 - Network Profiles
If we switch from Automatic to DefaultFixed, a message appears at the bottom of the Network Preferences screen warning us that the manual network configuration must be done using the dladm and ipadm commands, as shown in Figure 3.
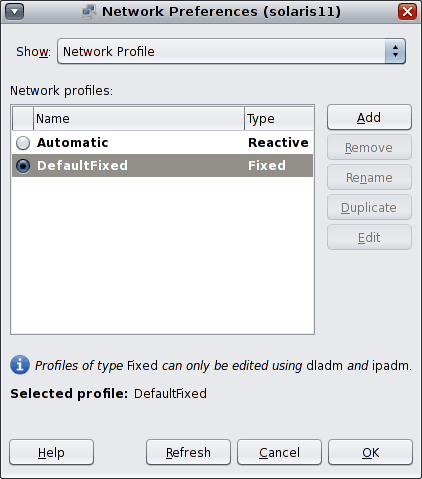
Figure 3 - Message at Bottom of Network Preferences Screen
The next option in the Show box is Wired (net0), which is shown in Figure 4:

Figure 4 - Wired(net0) Option in Showbox Screen
Here, there aren't any settings to configure; just some network information is shown.
Figure 5 shows the next screen: "How to edit Fixed network profiles."
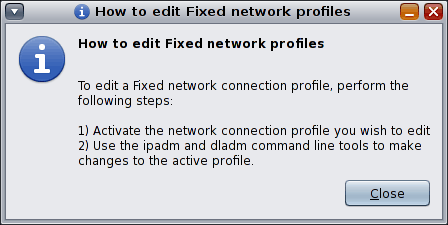
Figure 5 - How to Edit Fixed Network Profiles
We've already talked about configuring the network using the GUI versus using the command-line interface to manually configure the network. So now I should mention that there are four services responsible for network configuration in Oracle Solaris 11:
svc:/network/netcfg:defaultsvc:/network/loopback:defaultsvc:/network/location:defaultsvc:/network/physical:default
For now, it's essential to know that the last service (svc:/network/physical:default) is responsible for initializing the RNC framework. This fact can be proven using following commands:
# svcs -a | grep network/physical:default
online 15:20:01 svc:/network/physical:default
# svcs -p svc:/network/physical:default
STATE STIME FMRI
online 15:20:01 svc:/network/physical:default
15:19:55 617 nwamd
As you can see, the daemon that takes care of network configuration is the nwamd daemon. Although NWAM has been renamed to RNC, the daemon name was not changed.
You might be wondering how you can use the manual network configuration process to associate a fixed IP address to your network card without relying on RNC. I will show you a summarized procedure.
If you are using a SPARC-based platform, you need to ensure that all network interface cards (NICs) are using a unique MAC address by running the following commands:
# eeprom local-mac-address? = true
# reboot
# dladm show-linkprop -p mac-address
LINK PROPERTY PERM VALUE DEFAULT POSSIBLE
net0 mac-address rw 0:c:29:aa:c5:60 0:c:29:aa:c5:60 --
net1 mac-address rw 0:c:29:aa:c5:6a 0:c:29:aa:c5:6a --
From the output above, it looks like every NIC in the machine has a different MAC address. If we had two or more NICs with the same MAC address (for example, net1), we could execute following commands to change the MAC address for one of the network interfaces. For example, to change net1 MAC address, let's execute the following:
# dladm set-linkprop -p mac-address=00:11:22:33:44:55 net1
# reboot
Next, we will list all the profiles on our system:
# netadm list
TYPE PROFILE STATE
ncp Automatic online
ncu:phys net0 online
ncu:phys net1 online
ncu:ip net0 online
ncu:ip net1 online
ncp DefaultFixed disabled
loc Automatic online
loc NoNet offline
The active profile is Automatic. Changing it to DefaultFixed is easy; just run the following command:
# netadm enable -p ncp DefaultFixed
# netadm list
TYPE PROFILE STATE
ncp Automatic disabled
ncp DefaultFixed online
loc Automatic offline
loc NoNet online
If we needed to return to the Automatic profile (which uses the DHCP service by default), we would run the following command:
# netadm enable -p ncp Automatic
Now, let's see some other commands related to network configuration, and afterwards, we can learn how to do a manual configuration using a fixed IP address.
Sometimes it's necessary to know what our network cards are and what their properties are (full duplex, half duplex, speed, state, IP address, and so on). To get this information for the Automatic profile, we can execute commands shown in Listing 1:
# dladm show-phys
LINK MEDIA STATE SPEED DUPLEX DEVICE
net0 Ethernet up 1000 full e1000g0
net1 Ethernet up 1000 full e1000g1
# dladm show-ether
LINK PTYPE STATE AUTO SPEED-DUPLEX PAUSE
net0 current up yes 1G-f bi
net1 current up yes 1G-f bi
# ifconfig -a
lo0: flags=2001000849<UP,LOOPBACK,RUNNING,MULTICAST,IPv4,VIRTUAL> mtu 8232 index 1
inet 127.0.0.1 netmask ff000000
net0: flags=1004843<UP,BROADCAST,RUNNING,MULTICAST,DHCP,IPv4> mtu 1500 index 4
inet 192.168.1.105 netmask ffffff00 broadcast 192.168.1.255
ether 0:c:29:aa:c5:60
net1: flags=1004843<UP,BROADCAST,RUNNING,MULTICAST,DHCP,IPv4> mtu 1500 index 5
inet 192.168.1.106 netmask ffffff00 broadcast 192.168.1.255
ether 0:c:29:aa:c5:6a
lo0: flags=2002000849<UP,LOOPBACK,RUNNING,MULTICAST,IPv6,VIRTUAL> mtu 8252 index 1
inet6 ::1/128
net0: flags=20002004841<UP,RUNNING,MULTICAST,DHCP,IPv6> mtu 1500 index 4
inet6 fe80::20c:29ff:feaa:c560/10
ether 0:c:29:aa:c5:60
net1: flags=20002004841<UP,RUNNING,MULTICAST,DHCP,IPv6> mtu 1500 index 5
inet6 fe80::20c:29ff:feaa:c56a/10
ether 0:c:29:aa:c5:6a
Listing 1
Note: We can use the same commands with the DefaultFixed profile; however, in that case the output from the last command would be as follows:
lo0: flags=2001000849<UP,LOOPBACK,RUNNING,MULTICAST,IPv4,VIRTUAL> mtu 8232 index 1 inet 127.0.0.1 netmask ff000000
lo0: flags=2002000849<UP,LOOPBACK,RUNNING,MULTICAST,IPv6,VIRTUAL> mtu 8252 index 1 inet6 ::1/128
A similar thing occurs if we want to obtain information about any network interface objects on our system. For example, if we are using Automatic profile, the ipadm show-if command shows the following:
# ipadm show-if
IFNAME CLASS STATE ACTIVE OVER
lo0 loopback ok yes --
net0 ip ok yes --
net1 ip ok yes --
However, when are using DefaultFixed profile, the command shows this:
# ipadm show-if
IFNAME CLASS STATE ACTIVE OVER
lo0 loopback ok yes --
It's easy to see that RCN using the Automatic profile does all the work and, whereas when the system is using the DefaultFixed profile, only the loopback interface will be created. For example, the last command shows that we don't have any network interface to bind an IP address. How could we fix that?
Now let's do a manual network configuration on Oracle Solaris 11. Remember that we have net0 and net1 network interfaces on our system (we got this information from dladm show-phys). So, to accomplish our task, let's execute following steps:
To create an interface:
# ipadm create-ip net0
To bind an IP address to interface net0:
# ipadm create-addr -a 192.168.1.222/24 net0
To list interfaces:
# ipadm
NAME CLASS/TYPE STATE UNDER ADDR
lo0 loopback ok -- --
lo0/v4 static ok -- 127.0.0.1/8
lo0/v6 static ok -- ::1/128
net0 ip ok -- --
net0/v4 static ok -- 192.168.1.222/24
To associate a name to our IP address:
# echo "192.168.1.222 solaris11" >> /etc/hosts
To set a default gateway:
# route -p add default 192.168.1.1
To list our IP routes:
# netstat -rn
Routing Table: IPv4
Destination Gateway Flags Ref Use Interface
-------------------- -------------------- ----- ----- ---------- ---------
default 192.168.1.1 UG 14 1016
127.0.0.1 127.0.0.1 UH 2 42 lo0
192.168.1.0 192.168.1.222 U 3 1 net0
Routing Table: IPv6
Destination/Mask Gateway Flags Ref Use If
-------------------- ------ ------------- ------- ----- -------- -------
::1 ::1 UH 2 0 lo0
Previously, on Oracle Solaris 10, for set DNS resolution, all we had to do was run the following:
# cp /etc/nsswitch.dns /etc/nsswitch.conf
But, on Oracle Solaris 11, that doesn't work anymore. On Oracle Solaris 11, there's a new procedure for doing that. Initially, it seems a bit more complicated (as you'll see in the following commands), because the new procedure uses some concepts from the Service Management Facility that make a more-powerful and flexible whole name service mechanism. However, I'm sure you will become comfortable with this new service framework.
The new commands for setting our DNS name servers, our domain host, and our search domain list and then to configure Oracle Solaris 11 to include DNS resolution are as follows.
To set the DNS servers:
# svccfg -s svc:/network/dns/client setprop config/nameserver = net_address: "(8.8.8.8 8.8.4.4)"
To set our DNS domain:
# svccfg -s svc:/network/dns/client setprop config/domain = astring: '("example.com")'
To set the domain's search list:
# svccfg -s svc:/network/dns/client setprop config/search = astring: '("example.com")'
To set the IPv6 name resolution order:
# svccfg -s svc:/system/name-service/switch setprop config/ipnodes = astring: '("files dns")'
To set the IPv4 name resolution order:
# svccfg -s svc:/system/name-service/switch setprop config/host = astring: '("files dns")
Wow—that was a lot of work! What have we done so far? It's possible to check all parameters that we've set by running the two commands shown in Listing 2:
# svccfg -s svc:/network/dns/client listprop config
config application
config/value_authorization astring solaris.smf.value.name-service.dns.client
config/nameserver net_address 8.8.8.8 8.8.4.4
config/domain astring example.com
config/search string example.com
# svccfg -s svc:/system/name-service/switch listprop config
config application
config/default astring files
config/value_authorization astring solaris.smf.value.name-service.switch
config/host astring "files dns mdns"
config/printer astring "user files"
config/ipnodes astring "files dns"
config/hosts astring "files dns"
Listing 2
Nice! However, that's not enough. We need to ensure these settings take effect (now and after the next boot). To do that is straightforward. First, we should enable the DNS client, as shown in Listing 3:
# svcadm refresh svc:/network/dns/client
# svcadm restart svc:/network/dns/client
# more /etc/resolv.conf
#
# Copyright (c) 2013, Oracle and/or its affiliates. All rights reserved.
#
#
# _AUTOGENERATED_FROM_SMF_V1_
#
# WARNING: THIS FILE GENERATED FROM SMF DATA.
# DO NOT EDIT THIS FILE. EDITS WILL BE LOST.
# See resolv.conf(4) for details.
domain example.com
search example.com
nameserver 8.8.8.8
nameserver 8.8.4.4
Listing 3
Finally, we can use almost the same steps for name server resolution:
# svcadm refresh svc:/system/name-service/switch:default
# svcadm restart svc:/system/name-service/switch:default
# cat /etc/nsswitch.conf
# Copyright (c) 1991, 2013, Oracle and/or its affiliates. All rights reserved.
#
#
# _AUTOGENERATED_FROM_SMF_V1_
#
# WARNING: THIS FILE GENERATED FROM SMF DATA.
# DO NOT EDIT THIS FILE. EDITS WILL BE LOST.
# See nsswitch.conf(4) for details.
passwd: files
group: files
hosts: files dns mdns
ipnodes: files dns mdns
networks: files
protocols: files
rpc: files
ethers: files
netmasks: files
bootparams: files
publickey: files
netgroup: files
automount: files
aliases: files
services: files
printers: user files
project: files
auth_attr: files
prof_attr: files
tnrhtp: files
tnrhdb: files
Listing 4
Done. Our DNS servers and DNS resolution are configured. Now, for the next step, we can check our current IP address, as shown in Listing 5:
# ifconfig -a
lo0: flags=2001000849<UP,LOOPBACK,RUNNING,MULTICAST,IPv4,VIRTUAL> mtu 8232 index 1
inet 127.0.0.1 netmask ff000000
net0: flags=1000843<UP,BROADCAST,RUNNING,MULTICAST,IPv4> mtu 1500 index 2
inet 192.168.1.222 netmask ffffff00 broadcast 192.168.1.255
ether 0:c:29:aa:c5:60
lo0: flags=2002000849<UP,LOOPBACK,RUNNING,MULTICAST,IPv6,VIRTUAL> mtu 8252 index 1
inet6 ::1/128
net0: flags=20002000840<RUNNING,MULTICAST,IPv6> mtu 1500 index 2
inet6 ::/0
ether 0:c:29:aa:c5:60
Listing 5
Then, we can use the ping command to check that the system is alive, as shown in Listing 6:
# ping www.oracle.com
PING www.oracle.com: 56 data bytes
64 bytes from a23-62-166-140.deploy.akamaitechnologies.com (23.62.166.140): icmp_seq=0. time=143.691 ms
64 bytes from a23-62-166-140.deploy.akamaitechnologies.com (23.62.166.140): icmp_seq=1. time=142.495 ms
64 bytes from a23-62-166-140.deploy.akamaitechnologies.com (23.62.166.140): icmp_seq=2. time=141.506 ms
64 bytes from a23-62-166-140.deploy.akamaitechnologies.com (23.62.166.140): icmp_seq=3. time=141.732 ms
64 bytes from a23-62-166-140.deploy.akamaitechnologies.com (23.62.166.140): icmp_seq=4. time=142.020 ms
----www.oracle.com PING Statistics----
5 packets transmitted, 5 packets received, 0% packet loss
round-trip (ms) min/avg/max/stddev = 141.506/142.289/143.691/0.867
Listing 6
Great! Everything has worked as expected. However, what would we do if we wanted to accomplish the same task using a DHCP address without rely on RCN? Would that be possible? Yes, it would.
Let's do same steps using a DefaultFixed profile and a DHCP server. To illustrate the steps, we are going to take the other network interface (net1) and use it in a temporary way (using the -T option), as shown in Listing 7:
# ipadm create-ip net1
# ipadm create-addr -T dhcp net1
# ipadm
NAME CLASS/TYPE STATE UNDER ADDR
lo0 loopback ok -- --
lo0/v4 static ok -- 127.0.0.1/8
lo0/v6 static ok -- ::1/128
net0 ip ok -- --
net0/v4 static ok -- 192.168.1.222/24
net1 ip ok -- --
net1/v4 dhcp ok -- 192.168.1.106/24
Listing 7
Done. As we've wished, the net1 interface was configured successfully.
Oracle Solaris 11 Services
I must confess that when I saw the Service Management Facility in Oracle Solaris 10 (which is also part of Oracle Solaris 11), I was a little skeptical. I already knew about services from earlier Oracle Solaris releases and, honestly, I thought, "Why have they changed something that was so good?" This question arose around December 2004 during my first class about Oracle Solaris 10 (it was probably build 71). Sometime later, I realized the Oracle Solaris 10/Oracle Solaris 11 Service Management Facility is much better than any other service mechanism and much more powerful.
The Service Management Facility in Oracle Solaris 11 is controlled by a daemon named svc.startd, which is initiated from an entry in /etc/inittab, as shown below:
# more /etc/inittab
ap::sysinit:/usr/sbin/autopush -f /etc/iu.ap
smf::sysinit:/lib/svc/bin/svc.startd >/dev/msglog 2<>/dev/msglog </dev/console
p3:s1234:powerfail:/usr/sbin/shutdown -y -i5 -g0 >/dev/msglog 2<>/dev/msglog
In Oracle Solaris 9, the /etc/inittab file was much uglier; there were many more lines and the lines were more convoluted. Oracle Solaris 11 brings us a simpler /etc/inittab file in which just one line is really important: the line that starts the svc.startd daemon, which is responsible for initializing whole Oracle Solaris 11 Service Management Facility framework and its services.
To get a list of every Oracle Solaris 11 service, we would run the command shown in Listing 8:
# svcs -a | more
STATE STIME FMRI
legacy_run 18:30:07 lrc:/etc/rc2_d/S47pppd
legacy_run 18:30:07 lrc:/etc/rc2_d/S89PRESERVE
disabled 18:29:32 svc:/system/device/mpxio-upgrade:default
disabled 18:29:32 svc:/network/install:default
disabled 18:29:32 svc:/network/ipsec/ike:default
disabled 18:29:32 svc:/network/ipsec/manual-key:default
disabled 18:29:32 svc:/network/nis/domain:default
disabled 18:29:33 svc:/network/ipfilter:default
disabled 18:29:33 svc:/system/name-service-cache:default
disabled 18:29:33 svc:/network/nis/client:default
disabled 18:29:33 svc:/network/ldap/client:default
disabled 18:29:33 svc:/network/nfs/status:default
disabled 18:29:33 svc:/network/nfs/nlockmgr:default
disabled 18:29:33 svc:/network/nfs/cbd:default
disabled 18:29:33 svc:/system/idmap:default
disabled 18:29:33 svc:/network/nfs/mapid:default
disabled 18:29:33 svc:/network/rpc/keyserv:default
...
disabled 18:29:36 svc:/network/nfs/server:default
disabled 18:29:36 svc:/system/console-login:terma
disabled 18:29:36 svc:/system/console-login:termb
disabled 18:29:36 svc:/network/ldap/server:openldap_24
online 18:29:32 svc:/system/early-manifest-import:default
online 18:29:32 svc:/system/svc/restarter:default
online 18:29:34 svc:/network/sctp/congestion-control:cubic
online 18:29:34 svc:/network/sctp/congestion-control:vegas
online 18:29:34 svc:/network/sctp/congestion-control:newreno
online 18:29:34 svc:/network/sctp/congestion-control:highspeed
online 18:29:34 svc:/network/tcp/congestion-control:vegas
online 18:29:34 svc:/network/tcp/congestion-control:newreno
...
Listing 8
Wow! There are 224 services on my system! Some of them are disabled (not working) and others are online (enabled and working).
In the output in Listing 8, you can see some interesting columns:
- STATE shows the service status. Some possible values are
legacy_run(the service is using an old format and control such as run levels),disabled,online(running),maintenance(there is a configuration problem), andoffline(not running due to an unresolved service dependency). - STIME shows the start time of the service.
- FMRI (Fault Management Identifier) can be interpreted as a URL that serves to classify and distinguish the service in a unique way.
Let's take the cron service as an example. Finding out if this service is running or not is easy:
# svcs -a | grep cron
online 18:29:59 svc:/system/cron:default
As we can see, the cron service is online. Moreover, we can get other useful information about this service, as shown in Listing 9:
# svcs -l cron
fmri svc:/system/cron:default
name clock daemon (cron)
enabled true
state online
next_state none
state_time May 20, 2013 06:29:59 PM BRT
logfile /var/svc/log/system-cron:default.log
restarter svc:/system/svc/restarter:default
contract_id 88
manifest /etc/svc/profile/generic.xml
manifest /lib/svc/manifest/system/cron.xml
dependency require_all/none svc:/system/filesystem/local (online)
dependency require_all/none svc:/milestone/name-services (online)
Listing 9
The output in Listing 9 shows a lot of useful information. Another good command for determining what services cron depends on is the following:
# svcs -d cron
STATE STIME FMRI
online 18:29:57 svc:/milestone/name-services:default
online 18:29:59 svc:/system/filesystem/local:default
Finding out what services are dependent on cron service is also easy:
# svcs -D cron
STATE STIME FMRI
online 18:30:07 svc:/milestone/multi-user:default
And what are the processes initiated by cron? That is another good question that is easy to answer:
# svcs -p cron
STATE STIME FMRI
online 18:29:59 svc:/system/cron:default
18:29:59 768 cron
If we need to discover more details about the cron service and gather additional information, we could use the following command:
# svcs -x cron
svc:/system/cron:default (clock daemon (cron))
State: online since May 20, 2013 06:29:59 PM BRT
See: cron(1M)
See: crontab(1)
See: /var/svc/log/system-cron:default.log
Impact: None.
So far, so good. Until now, we have used a lot of service commands and we've gathered tons of information about our services on Oracle Solaris 11, but if we need to change the service state? Table 1 shows a summary of some additional commands:
Table 1
| Goal | Command |
|---|---|
| Disable a service | # svcadm disable <fmri> |
| Temporarily disable a service | # svcadm -t disable <fmri> |
| Enable a service | # svcadm enable <fmri> |
| Recursively enable a service | # svcadm -r enable <fmri> |
| Restart a service | # svcadm restart <fmri> |
| Refresh a service configuration | # svcadm refresh <fmri> |
| Take a service out of maintenance | # svcadm clear <fmri> |
If you don't like using the service commands, that's OK. You can use a great GUI service tool introduced in Oracle Solaris 11 (see Figure 6). You can find it by selecting System -> Administration -> SMF Services. There, you can execute the same tasks that you've performed using the command-line interface.
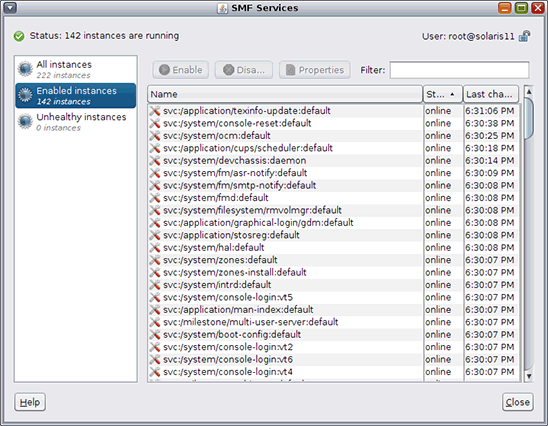
Figure 6 - Managing SMF Services Through the GUI
Oracle Solaris 11 Image Packing System
Now, I'd like to explain some basic concepts about package management, which has changed a lot since Oracle Solaris 10. Do you remember pkgadd, pkgrm, and pkginfo? Congratulations, but I hope you never need them again!
Introduced in Oracle Solaris 11, the Image Packaging System is a very powerful, simple, and useful way to manage packages, both from a command-line interface and a GUI tool.
Before talking about the packages themselves, let's discuss updates. Every operating system needs patches and Oracle Solaris 11 is no different. To update Oracle Solaris 11, select System -> Administration -> Update Manager, which bring up the Update Manager shown in Figure 7.

Figure 7 - Update Manager GUI
You might recall that we did not register our Oracle Solaris 11 installation after installing it in Part 1. Furthermore, according to Figure 7, there are no updates from the Oracle repository at this time. If we had an Oracle Support agreement, we could change our configured repository to point to the Oracle Support Repository, but that is beyond the scope of this article.
It's easy to manage packages on Oracle Solaris 11. First, select System -> Administration -> Package Manager to open the Package Manager shown in Figure 8.

Figure 8 - Package Manager GUI
As an exercise, let's search for and install a package. Since I love security articles and tools, I will show how we can install the nmap tool. First, we should search for the nmap package in the Oracle repository, as shown in Figure 9, to confirm that it is available:

Figure 9 - Searching for the nmap Package in the Package Repository
We found the nmap package. Next, let's install it. To do that, first ensure the checkbox next to the nmap package is selected. Then click the Install/Update button. The screen shown in Figure 10 appears.
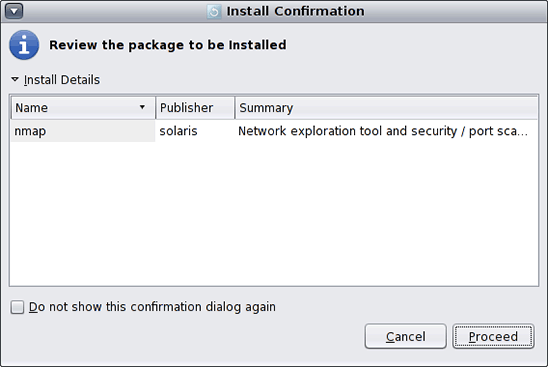
Figure 10 - After Clicking the Install Update Button
If you are happy with your choice, click Proceed. The package is downloaded and installed, as shown in Figure 11.

Figure 11 - The Package Has Been Downloaded and Installed
Our nmap package was installed successfully, as shown in Figure 12:
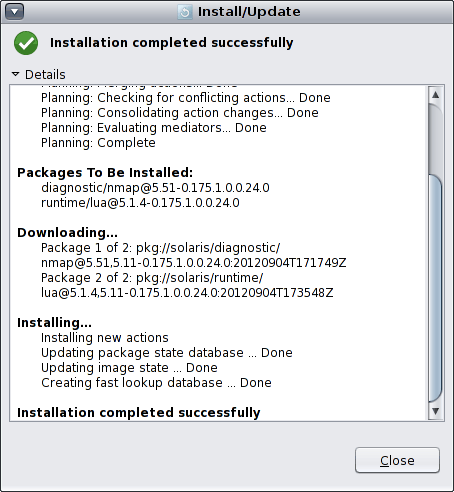
Figure 12 - Message Confirming Successful Installation
Nevertheless, many people prefer to manage packages from the command-line interface. Let's learn some useful commands.
For example, to check whether the nmap package is available in the Oracle repository, run the command shown in Listing 10:
# pkg search nmap
INDEX ACTION VALUE PACKAGE
pkg.description set Nmap is useful for inventorying the network, managing service upgrade schedules, and
monitoring host or service uptime. pkg:/diagnostic/nmap@5.51-0.175.1.0.0.24.0
basename file usr/bin/nmap pkg:/diagnostic/nmap@5.51-0.175.1.0.0.24.0
pkg.fmri set solaris/diagnostic/nmap pkg:/diagnostic/nmap@5.51-0.175.1.0.0.24.0
basename dir usr/share/nmap pkg:/diagnostic/nmap@5.51-0.175.1.0.0.24.0
Listing 10
We've already installed this package, but we could do this (if needed) using either of the following commands:
# pkg install nmap
# pkg update nmap
To verify whether our package installation was done successfully, we can use the following command:
# pkg verify nmap
Just in case something went wrong, we can fix it:
# pkg fix --accept nmap
Sometimes, you need to list a package's content. This can be done using the command shown in Listing 11:
# pkg contents nmap
PATH
usr
usr/bin
usr/bin/ncat
usr/bin/ndiff
usr/bin/nmap
usr/bin/nmapfe
usr/bin/nping
usr/bin/xnmap
usr/bin/zenmap
usr/lib
usr/lib/python2.6
usr/lib/python2.6/vendor-packages
usr/lib/python2.6/vendor-packages/radialnet
usr/lib/python2.6/vendor-packages/radialnet/__init__.py
usr/lib/python2.6/vendor-packages/radialnet/__init__.pyc
usr/lib/python2.6/vendor-packages/radialnet/bestwidgets
usr/lib/python2.6/vendor-packages/radialnet/bestwidgets/__init__.py
...
Listing 11
When we want to uninstall a package, we can do the following:
# pkg uninstall nmap
To collect information about our nmap package, we can run the command shown in Listing 12:
# pkg info nmap
Name: diagnostic/nmap
Summary: Network exploration tool and security / port scanner.
Description: Nmap is useful for inventorying the network, managing service
upgrade schedules, and monitoring host or service uptime.
Category: System/Administration and Configuration
State: Installed
Publisher: solaris
Version: 5.51
Build Release: 5.11
Branch: 0.175.1.0.0.24.0
Packaging Date: September 4, 2012 05:17:49 PM
Size: 12.28 MB
FMRI: pkg://solaris/diagnostic/nmap@5.51,5.11-0.175.1.0.0.24.0:20120904T171749Z
Listing 12
The package license can be verified using the following command:
# pkg info --license nmap
To examine what package operations were executed previously, use the command shown in Listing 13, which is a nice way to keep track of all the package operations that have been done on our system:
# pkg history
START OPERATION CLIENT OUTCOME
2012-09-19T16:48:22 set-property transfer module Succeeded
2012-09-19T16:48:22 add-publisher transfer module Succeeded
2012-09-19T16:48:22 refresh-publishers transfer module Succeeded
2012-09-19T16:48:22 image-create transfer module Succeeded
2012-09-19T16:48:30 rebuild-image-catalogs transfer module Succeeded
2012-09-19T16:48:36 set-property transfer module Succeeded
2012-09-19T16:48:37 install transfer module Succeeded
2012-09-19T17:30:12 update-publisher transfer module Succeeded
2012-09-19T17:30:12 refresh-publishers transfer module Succeeded
2012-09-19T17:30:16 rebuild-image-catalogs transfer module Succeeded
2013-05-19T17:20:26 uninstall transfer module Succeeded
2013-05-20T00:47:07 refresh-publishers pkg Succeeded
2013-05-20T00:47:14 rebuild-image-catalogs pkg Succeeded
2013-05-21T00:33:54 refresh-publishers packagemanager Succeeded
2013-05-21T00:33:58 rebuild-image-catalogs packagemanager Succeeded
2013-05-21T00:37:06 install packagemanager Succeeded
Listing 13
If you want to clear this history, run this command:
# pkg purge-history
Conclusion
I hope you have learned a lot from this series of articles. As we've seen, Oracle Solaris 11 is an outstanding operating system, and we have a lot of things to learn. In my opinion, Oracle Solaris is the most secure, powerful, complete, and fast operating system in the world, and I'm sure you will think the same soon.
As John Milton said in 1667 in Paradise Lost, said "Long is the way, and hard, that out of hell leads up to light." I hope to see you soon.
See Also
- Part 1 of this series, "Exploring Installation Options and User Roles in Oracle Solaris 11"
- Links to articles Alexandre Borges has published in Portuguese in Linux Magazine Brazil
- Links to columns Alexandre Borges has published in Portuguese in Linux Magazine Brazil
About the Author
Alexandre Borges is an Oracle ACE and who worked as an employee and contracted instructor at Sun Microsystems from 2001 to 2010 teaching Oracle Solaris, Oracle Solaris Cluster, Oracle Solaris security, Java EE, Sun hardware, and MySQL courses. Nowadays, he teaches classes for Symantec, Oracle partners, and EC-Council, and he teaches several very specialized classes about information security. In addition, he is a regular writer and columnist at Linux Magazine Brazil.
Revision 1.0, 08/27/2013