Sovereign Cloud
Meet your requirements for location, access, data residency, and operational controls without compromising cloud services, SLAs, or pricing with Oracle Cloud Infrastructure (OCI) solutions for sovereignty.
Learn about the five key pillars of sovereign AI.
Why sovereign cloud?
Maintain control over your operations and assets in the cloud to ensure productivity and resilience while retaining a competitive advantage.
-
Meet evolving compliance, legal, and regulatory needs
With the ability to audit and report, customize compliance, and control IT systems.
-
Restrict access to data and operational information flows
With a distributed cloud approach, smart access and governance capabilities, and region and operations isolation.
-
Operate in the cloud, isolated from others and the internet
Without additional spending and compromising on technology.
-
Address AI sovereignty needs for data and AI infrastructure
With Oracle’s full AI stack in the public cloud or in your data center.
Sovereign cloud—Oracle meets you where you are
Achieving sovereignty requires more than a one-size-fits-all solution. Depending on your organization and where it operates, you may have different needs in different locations. OCI offers flexible solution options built off the same platform. Get the same cloud services, APIs, and SLAs at the same price point, regardless of whether you need to achieve compliance in the public cloud, have completely isolated lights-out operations, or accommodate any scenario in between.
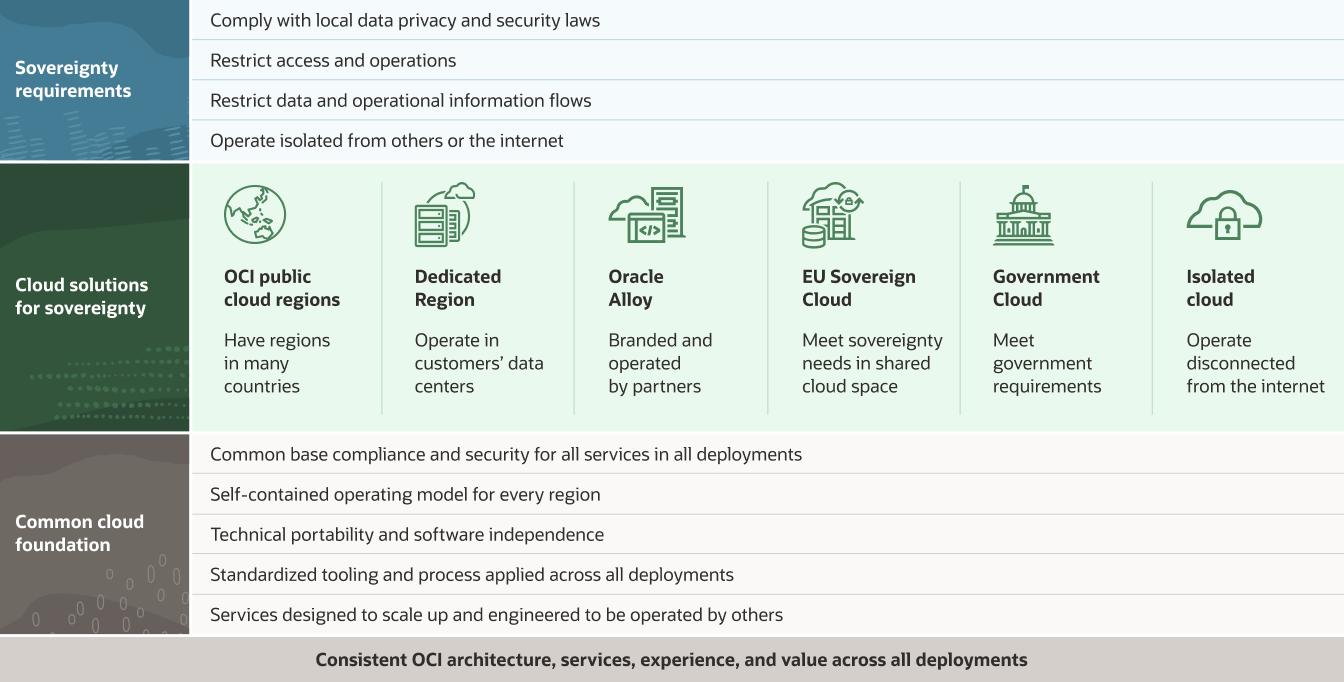
Oracle Cloud Infrastructure’s sovereign cloud solutions
-
![]()
EU Sovereign Cloud
Oracle EU Sovereign Cloud offers more than 200 of the same services as Oracle’s public cloud. These are physically separated cloud regions located and operated entirely within the European Union and aligned with EU standards of practice.
Learn more about EU Sovereign Cloud -
![]()
Government Cloud
Oracle Cloud operates government cloud regions that are isolated from commercial customers. Designed for public sector agencies in the United States, UK, and Australia, the regions meet data sovereignty requirements for public sector while offering same set of services, support, and billing as OCI’s public cloud.
Learn more about Government Cloud -
![]()
Dedicated Region
An independent, complete cloud region in a customer-defined data center, with both data and control planes on-premises to meet data residency and low-latency requirements.
Learn more about Dedicated Region Cloud@Customer -
![]()
Isolated cloud
Secure, air-gapped regions designed to meet the highest demands of global customers’ mission-critical classified workloads.
Learn more about Isolated cloud -
![]()
OCI public cloud regions
Oracle Cloud spans more than 35 interconnected commercial regions across 24 countries. The multiple geographically separated regions within one country provide more control over data residency for customers to achieve local compliance and implement disaster recovery.
Learn more about OCI public cloud regions -
![]()
Oracle Alloy
Oracle Alloy enables partners to become in-country cloud providers and offer a robust cloud ecosystem to their local customers while fulfilling digital sovereignty and regulatory compliance requirements.
Learn more about Oracle Alloy
Sovereign cloud use cases
Due to the increasing pressure from industry and regional regulators and geopolitical events, sovereignty in the cloud has become an important consideration not only for the public sector but also for private enterprises.
Compliant cloud for winning customer trust
Organizations proactively prioritizing compliance gain a competitive edge and build a reputation for trustworthiness and ethical operations. All Oracle Cloud services are designed to meet various compliance standards and the highest levels of security—all the way up to Top Secret levels across all deployment models.
National Pharmacies enhances customer loyalty and lowers cost of compliance
Adopting compliant cloud disaster recovery to enhance business continuity
Cloud backup and disaster recovery provides reliable methods to secure all types of sensitive data from infrastructure failures and malicious attacks. Oracle’s distributed cloud services enable various methods and topologies for data and applications—in the cloud, on-premises, or using hybrid approach. Oracle’s multi-region realm setup helps achieve a greater degree of sovereignty.
Applying a distributed cloud strategy to meet regulatory needs
By leveraging a distributed cloud infrastructure, organizations can meet compliance requirements while benefiting from the scalability and flexibility of cloud computing. Oracle’s distributed cloud services offer you more options to control your data, ensuring data sovereignty and security.
Oracle' distributed cloud delivers more choices to customers worldwide
Highly regulated industries
Secure data and protect patient privacy in the cloud
Healthcare organizations can better adapt to modern challenges with the cloud. With solutions such as a data lakehouse, AI, and machine learning (ML), electronic health record (EHR) data is no longer siloed, televisits can be utilized at scale, and organizations can rapidly respond to changes in supply and regulations. Oracle Cloud services regularly undergo independent third-party audits, including ISO 27000 series, SOC, HDS, HIPAA, and HITRUST.
Maintain complete control over data and financial governance
The financial services industry is one of the most demanding in terms of regulation and security. Financial transactions require high-performance processing and architectures that enable stable operations. Specialized on-premises cloud solutions such as Oracle Cloud Infrastructure (OCI) Dedicated Region and Oracle Alloy continue to deliver greater business value to our customers faster and easier than ever before while maintaining stringent levels of control and governance.
End-to-end policy and control over applications and infrastructure from core to edge
Distributed cloud architecture allows telcos to store and process data in a geographically distributed manner to improve performance by reducing latency, improving data access times, and achieving greater sovereignty by storing data in compliance with local regulations and data protection laws. Oracle’s distributed cloud services can help telcos achieve both performance and sovereignty.
Telecommunication:
Unlocking 5G with end-to-end distributed cloud
Governments across the globe
Cloud regions optimized for scale, designed with security first, aligned with a nation’s security initiatives
The U.S. Department of Defense, UK Government and Defence, and the Australian Government and Defence cloud regions are sovereign, dedicated cloud regions designed in collaboration with local defense and government agencies to meet data sovereignty requirements and access a complete cloud infrastructure platform supporting highly secret and top secret, classified, and mission-critical workloads.
Boost public sector innovation and help ensure data sovereignty
Many government agencies have selected OCI Dedicated Region to accelerate digital transformation. Between the new services and the data sovereignty offerings, OCI Dedicated Region is strengthening government digital infrastructure for the modern economy.
Sultanate of Oman and Oracle Extend Collaboration to Establish Oman’s First Hyperscale Cloud Region
Protect mission-critical workloads with OCI’s dedicated two-region model
Mission continuity is essential for global customers entrusted with highly classified, sensitive data. Oracle Cloud Infrastructure’s two-region deployment strategy enables you to deploy resilient services in multiple geographically separated locations within the same national/regional borders to help you build true business continuity and disaster protection and meet regulatory and sovereignty requirements.

OCI’s distributed cloud: Cloud services everywhere you need them
Expanding cloud options for customers with more public cloud, multicloud, hybrid cloud, and dedicated cloud capabilities.
Get started with EU Sovereign Cloud
Contact sales
Contact us to learn more about EU Sovereign Cloud and let one of our experts help.
-
They can answer questions such as
- What workloads run best on OCI?
- How do I get the most out of my overall Oracle investments?
- How does OCI compare to other providers?
Get expert perspectives
Learn more about your options in the cloud from industry analysts. They provide detailed, objective perspectives on the latest strategies and solutions.





