The Intercept’s “Reporting” on Oracle is Little More than Association by Innuendo
On February 18, The Intercept published a breathless 4,965-word “SCOOP” entitled “How Oracle Sells Repression in China,” which purported to show Oracle aiding and abetting the Chinese government and police agencies in repressing citizens. Whatever this story is, and frankly I’m still not sure even after several dozen reads, it is deeply at odds with reality.
The Intercept story features the obligatory Getty and UPI stock photos of surveillance in China, despite the fact that these photos have zero to do with Oracle. It has pull quotes from “experts” with no first-hand knowledge of Oracle’s business. It calls out to another “related” story stating that “millions of leaked police files detail suffocating surveillance of China’s Uyghur minority” with a “massive Chinese police database.” Click on this “related” story (which is linked twice) and you find…not a single reference to Oracle. The Intercept story then links to President Xi preserving “stability by guarding against black swan events,” with no reference whatsoever to Oracle. The story links to a study of China’s Golden Projects entitled “China’s Golden Shield: Corporations and the Development of Surveillance Technology in the People’s Republic of China.” Wait for it: Not a single mention of Oracle. The story links to yet another story about Brazil’s government “working tirelessly to merge information and create mega-databases” of citizens. Again, click through and you see... no mention of Oracle. There’s the paragraph about the UAE “eyes” program, which involves “5,000 surveillance cameras” for “police to track people throughout the city”... follow the link, no connection to Oracle. Of course, no story about repression would be complete without references to Edward Snowden, but again, not even a remote connection to Oracle. The whole story is an endless innuendo loop linking itself to 6 other Intercept stories, all with nothing to do with Oracle.
For those who aren’t counting, there were 62 unique links in the article. In fact, The Intercept story links to dozens of documents and articles that have nothing to do with Oracle. Or with China for that matter. It is a veritable hodgepodge of links. One link that does reference Oracle is an article about Oracle Exadata product placement in Iron Man 3 (I’m not kidding). One can imagine the author studding the article with blue hypertext to bolster the credibility of her thesis, or maybe it was just to improve the article’s search score. If you do follow the links down the rabbit hole, you’ll see they don’t amount to anything near what she alleges and are almost entirely unrelated to Oracle.
What the story doesn’t mention is that for over a decade while all of Oracle’s competitors have been substantially increasing investment and “partnerships” in China, Oracle has been substantially reducing our presence in China. We won’t name names, but you know who you are. You will not find an Oracle Cloud region in China, or an Artificial Intelligence center, or an R&D center, or a Joint Innovation Center. You won’t see any evidence that we open sourced our code for free use in China, including by the military. You’ll notice that we don’t have joint “training” centers. Back in 2015 you will notice that while nearly every single technology CEO was in Seattle posing for a photo op with President Xi, Oracle declined to participate. As the New York Times noted, “looking back at the trip, the most memorable moment—and maybe the most important—was watching $2.5 trillion of American corporate power pay homage to the Chinese President.” Pictures speak 4,965 words.
As proof that Oracle is involved in work for defense, intelligence and police, The Intercept references our work for the U.S. Intelligence Community, the U.S. Department of Defense, the Chicago Police Department and the Illinois State Police. While we understand The Intercept’s editorial views, we are proud and unapologetic about our national security work in the United States and in like-minded countries around the world. And while the story is ostensibly about repression in China, last we checked Chicago and Illinois are squarely within the four corners of the United States.
Now, let’s move to the smoking gun(s): A series of PowerPoint presentations (or “pitch decks”) purportedly proposing Oracle solutions in China. Of course, this is not a case of confidential documents leaked to The Intercept in the dark of the night because every single one of these PowerPoints was publicly available on Oracle’s website. The Intercept has virtually no evidence that any of these “pitches” were ever actually implemented in any form whatsoever. And The Intercept fully understands that these PowerPoints don’t even portray actual, implementable solutions.
The fact is that Oracle has a world class export compliance program. We work very hard to ensure that we are not only in strict compliance with export controls and sanctions but that both end users and end uses of our software are consistent with our very public position to have a very small footprint in China. We strongly condemn political repression in all its forms, and despite The Intercept’s association by innuendo, it does not provide a single example in the story of Oracle software actually being used in the manner The Intercept suggests.
We certainly wish these PowerPoint pitches didn’t exist because these kinds of end users and end uses would not be approved by Oracle anyway, if they ever advanced to an actual proposed transaction. But with 140,000 employees around the world, it is nearly impossible to control for every PowerPoint created by every one of them, unless we start tracking employee keystrokes (which we assume The Intercept would oppose). And The Intercept understands the difference between a PowerPoint and an actual proposal with pricing, implementation schedules, partners, and specific product SKUs. And The Intercept further understands what a license agreement and contract look like. But the sum total of all the evidence for this story is “pitch decks,” which, by the way, were most likely never even pitched.
The PowerPoint presentations do not support the thesis that Oracle deployed repression-aiding systems in the way The Intercept alleges. The supposed government customers are simply logos, with no reference of any kind to what these customers might be using. The opening two paragraphs of the story rely on a PowerPoint that is clearly a hypothetical case study. The best—and only—human source for the story can’t even remember what agency or province used the software mentioned in one alleged instance. No individual end user or organization confirms the account.
The only other Oracle-related source is a former employee, Hong Eng-Koh, who apparently won’t return The Intercept’s emails or LinkedIn messages. Mr. Koh left Oracle in 2016 for Huawei. Under the heading “Selling to Xinjiang,” The Intercept starts with a recitation of Huawei—not Oracle’s—work. Apparently after leaving Oracle, Mr. Koh at Huawei “hawks an analytics platform called FusionInsight (PDF).” Also, after leaving Oracle, Mr. Koh reportedly “supplied Sao Paulo with of hundreds of surveillance cameras.” There are also evidently news accounts of Mr. Koh “speaking on behalf of Huawei after the company helped supply a controversial facial recognition system...used at Rio’s famed Carnival in 2019 where an innocent person was arrested.” We are certainly not condoning Mr. Koh’s work for Huawei after he left Oracle, but we are at a loss to understand how The Intercept thinks this current work at Huawei by a former employee has anything to do with us.
Results-Oriented Innuendo
The reason for The Intercept’s reliance on association by innuendo—as opposed to actual evidence—is The Intercept’s own fault. Oracle was contacted by Intercept reporter Mara Hvistendahl on Thursday, February 11. In classic gotcha journalism fashion the reporter conveyed over email that her reporting was “completed” meaning she had already cemented both her premise and her conclusions. She said she was seeking comment on “Oracle’s work outside the U.S.” and gave us until Monday, February 15 (a holiday, btw) to respond. She was not willing to actually speak to us on the phone, she returned emails timestamped 2:00 am PT, and anything we wanted to say—including to merely understand what she was writing—would have to be fully on the record. After some e-mail prodding, Ms. Hvistendahl sent us a set of questions, which we responded to in writing and fully on the record. In fact, we provided more than 2,000 words of on-the-record comments, most of which never made her story. Here’s one exchange:
- Intercept: We have come across dozens of Oracle slide presentations that say Oracle has sold data analytics software to Chinese police and unnamed other products to the Chinese military and defense contractors.
- Oracle on the record response: Oracle is not selling data analytics software nor any other products or services, including support, to Chinese police or to Chinese military and defense contractors for any end-uses implied in the materials you provided. Our products and services are not designed, developed, deployed, or supported for these purposes in China. Such activities would be considered inconsistent with Oracle’s core Corporate Citizenship Values (also on our Website), including our Human Rights statement (also on our Website (PDF)).
We’ve conducted a preliminary review of the material you provided as well as what’s in the public domain in general, including on Oracle’s external website. We found no actual implementations of the nature you suggest. - Intercept Follow-up: When you say you found no actual implementations of the nature we suggest, how would you know if software is being used in a particular manner? Do you audit the use of your software?
- Oracle on the record response: We are confident in our response to The Intercept. We know exactly what we sell and support and all parties to transaction as a matter of standard corporate practice, per our extensive support, compliance, and due diligence policies and processes. At time of transaction we ensure the products and services requested by high-risk/red-flag end-users, including those of the type you’re inquiring about, are consistent with the stated end-use, industry, and even end-user location(s). Anomalous product configurations, quantities, versions, and other such factors are part of a standard review process. Post transaction, most Oracle implementations include product support, which if provided by Oracle ensures an ongoing direct support relationship with our customers, also affording an understanding of a customer’s implementations.
We really aren’t sure how we could have been clearer. We then attempted numerous times to contact Ms. Hvistendahl’s editor, Ryan Tate, by phone and email. Mr. Tate didn’t even acknowledge the calls, let alone speak to us. “Ghosted,” as they say. So, this 4,695-word feature was published without a single actual discussion with Oracle.
The Intercept is extremely sensitive to our suggestion that this entire story looks like it was provided by a competitor, so we won’t restate that charge here. But with scant actual evidence, with strong and clear on-the-record responses, with a total unwillingness of the reporter and editor to even talk with us about the story, with a story littered with unrelated innuendo and detours to nowhere (like TikTok), with dozens of links to wholly unrelated (to Oracle) acts of repression, The Intercept published it anyway.
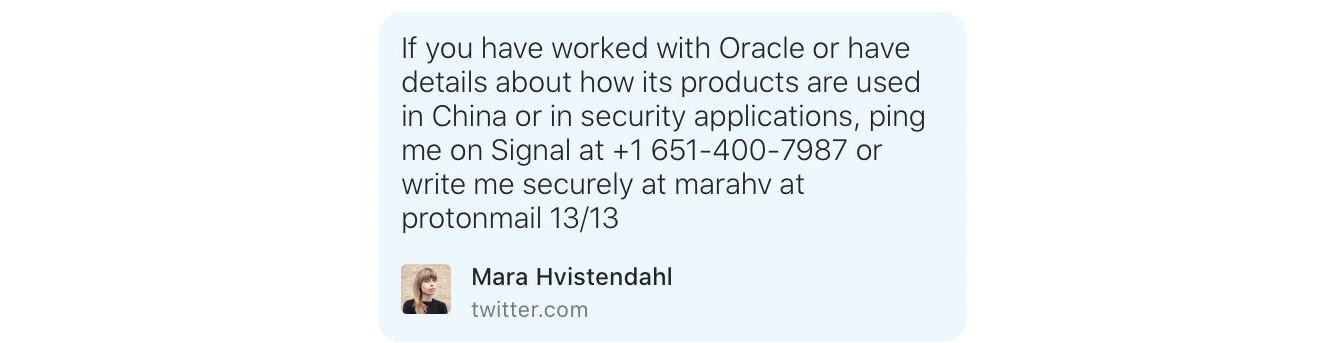
Because we have now very publicly criticized the story, we are confident The Intercept will leave no stone unturned to prove us wrong. So, for efficiency’s sake, I’ll restate the author’s contact information here:
We confirmed for The Intercept that the PowerPoints were authentic. And I will concede upfront that it is certainly possible that Oracle software may have found its way somewhere into the Chinese police state for unauthorized use. That could be because the software is pirated. It could be that the software is unlicensed. It could be that the end user or end use was misrepresented. Or, yes, something could have slipped through the cracks.
But the notion that Oracle is involved in any kind of systematic selling of our software to aid in repression in China is completely unfounded, belied by the very public facts on the ground, and completely untrue. Notwithstanding the nearly 5,000 words already written by the time Oracle was contacted, this story never should have been published.