What Is a WAF (Web Application Firewall)?
June 24, 2021
Web Application Firewall Definition
Web application firewalls help protect web applications from malicious attacks and unwanted internet traffic, including bots, injection and application-layer denial of service (DoS). The WAF will help you establish and manage rules for avoiding internet threats, including IP addresses, HTTP headers, HTTP body, URI strings, cross-site scripting (XSS), SQL injection, and other OWASP-defined vulnerabilities. Web application firewall are deployed to protect web-facing applications and collect access logs for compliance, and analytics.
Why Is WAF Security Important?
Web application firewalls help protect applications deployed in the public cloud, on-premises, and in multicloud environments with access controls based on geolocation data, whitelisted, and backlisted IP addresses, Hypertext Transfer Protocol Uniform Resource Locater (HTTP URL), and HTTP header. WAFs can identify and block malicious bot traffic with an advanced set of verification methods, inducing JavaScript, Completely Automated Public Turing Test to tell Computers and Humans Apart (CAPTCHA), device interpreting, and human interaction algorithms. WAFs protect internet-facing applications from attacks as a result of integrated threat intelligence that aggregates from multiple sources and Open Web Application Security Project (OWASP) detection rules.
Web Application Firewall Service Components
There are a number of components of the WAF, notably:
Web application firewall policy
WAF policies encompass the overall configuration of your WAF service, including origin management, protection rule settings, and bot detection features.Origin
Your web application's origin host server, designed to set up protection rules or other features, as defined in your WAF policy.Protection rules
Protection rules can be configured to either allow, block, or log network requests when they meet the specified criteria of a protection rule. The WAF will observe traffic to your web application over time and suggest new rules to apply.Bot management
The WAF service includes several features that allow you to detect and either block or allow identified bot traffic to your web applications. Bot management features include JavaScript challenge, CAPTCHA challenge, and GoodBot whitelists. Bot management solutions can use detection techniques such as IP rate limiting, CAPTCHA, device fingerprinting, and human interaction challenges to identify and block suspicious bot activity in your web applications. At the same time, WAF can allow legitimate bot traffic from published bot providers to bypass these controls.
Features of Web Application Firewalls
Some of the key capabilities and features of WAFs include:
- Dynamic traffic routing via domain name system (DNS): Leverages DNS-based traffic-routing algorithms that consider user latency from thousands of global locations to determine the lowest latency routes.
- High availability of the WAF services: When configuring web-application delivery, WAFs can offer several high availability configuration options with the ability to add multiple origin servers. These settings can be used in cases where primary origin servers are offline or not responding correctly to health checks.
- Flexible methods to managing policies: WAF configurations allow you to configure and manage features and functionality to address your organization’s needs.
- Monitoring and reporting: WAFs give users the ability to access reporting related to their content library for compliance and analysis.
- Escalation: Information from WAFs provide support teams the ability to issue and escalate a ticket depending on urgency.
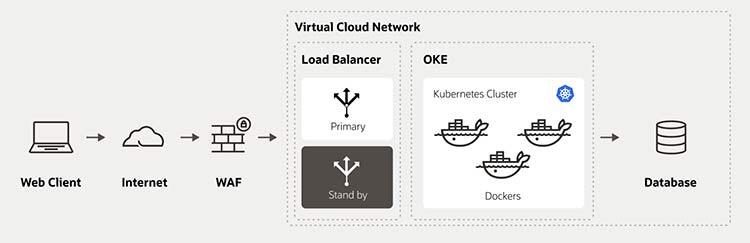
Deploying a Cloud Based Web Application Firewall
A cloud based WAF must support multiple web application hosting environments including on-premises, cloud, hybrid, and multi-cloud. Meaning, a WAF can protect a network edge from malicious traffic regardless of how many infrastructure providers are used. The right cloud based WAF will provide an independent platform for securing all internet facing applications and APIs, no matter where they reside.
The best cloud based WAFs are managed 24/7 by a team of experienced internet security experts who monitor an environment and recommend proven threat mitigation steps when issues arise. The benefits of a managed WAF service include significant risk reduction. The burden of management is also reduced due to WAF configuration, monitoring, tuning, and incident response as the responsibility of the cloud provider. Continuous monitoring protects organizations from unplanned downtime and the resulting damage to a brands reputation. Additionally, managed services enable more time to be focused on core business tasks and improving the bottom line. Cloud-based WAFs provide the highest level of web application security without a major upfront investment in resources or ongoing costs related to maintenance, hardware replacement, and software upgrades. Cloud-based WAFs offer ease of deployment and predictable subscription pricing, which makes budget planning easier.
Benefits of Web Application Firewalls
The Web Application Firewall (WAF) filters out malicious requests to a web application or API. It also provides more visibility as to where the traffic is coming from—and Layer 7 distributed denial of service (DDos) attacks are mitigated, to help gain application availability, and better enforce compliance mandates.
The bot management solution uses detection techniques such as IP rate limiting, CAPTCHA, device fingerprinting, and human interaction challenges to identify and block bad and/ or suspicious bot activity from scraping your website for competitive data. At the same time, the WAF can allow legitimate bot traffic from Google, Facebook, and others to continue to access your web applications as intended. WAF employs an intelligent Domain Name System (DNS) using a data-driven algorithm that determines the best global point of presence (POP) to serve a given user in real time. As a result, users are routed around global network issues and potential latency while offering the best possible uptime and service levels.
Try Oracle Cloud Storage for Free
A free Oracle Cloud account enables access to a number of Always Free services, including two Oracle Autonomous Databases and a range of other features. These Always Free resources are available without time constraints without interruption.