Oracle Risk Management and Compliance
Proactively protect your enterprise to build trust and resilience amid constant change and disruption. Oracle Fusion Cloud Risk Management and Compliance is a security and audit solution that controls user access to your Oracle Cloud ERP financial data, monitors user activity, and makes it easier to meet compliance regulations through automation.
Learn how to empower employees and drive a risk aware culture with embedded AI.
Risk Management and Compliance use cases
Improve cybersecurity posture
Prevent unauthorized permissions and access
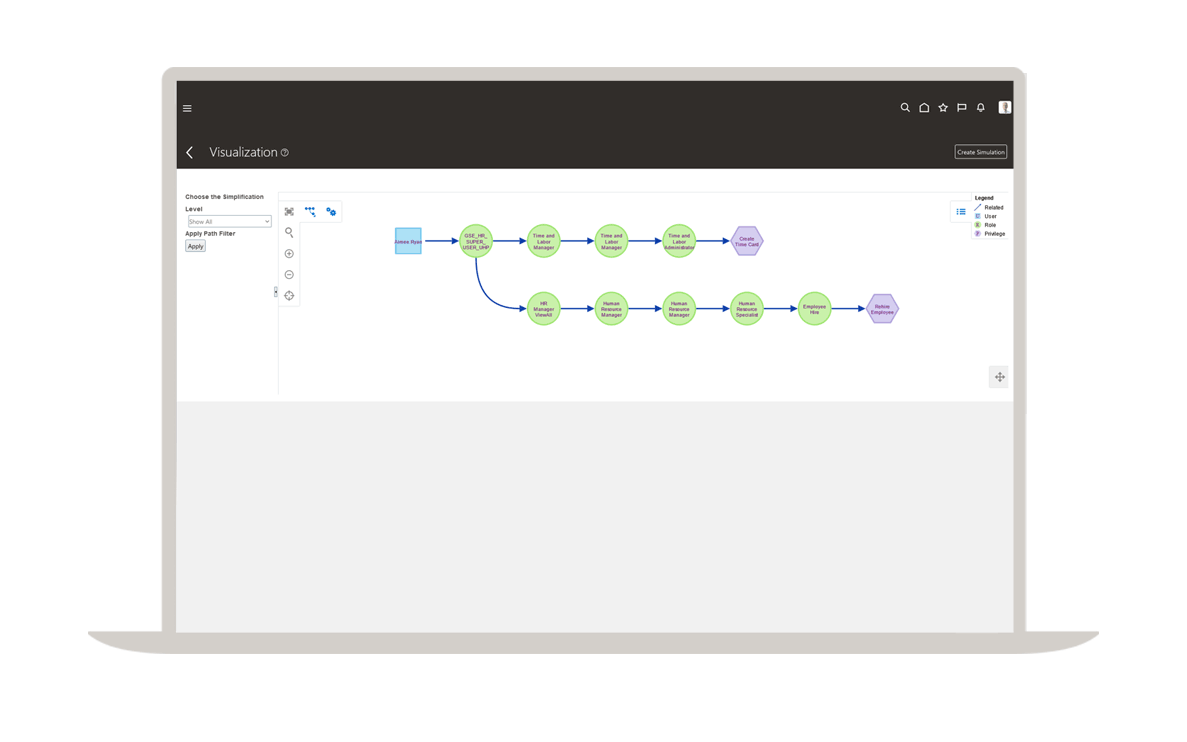
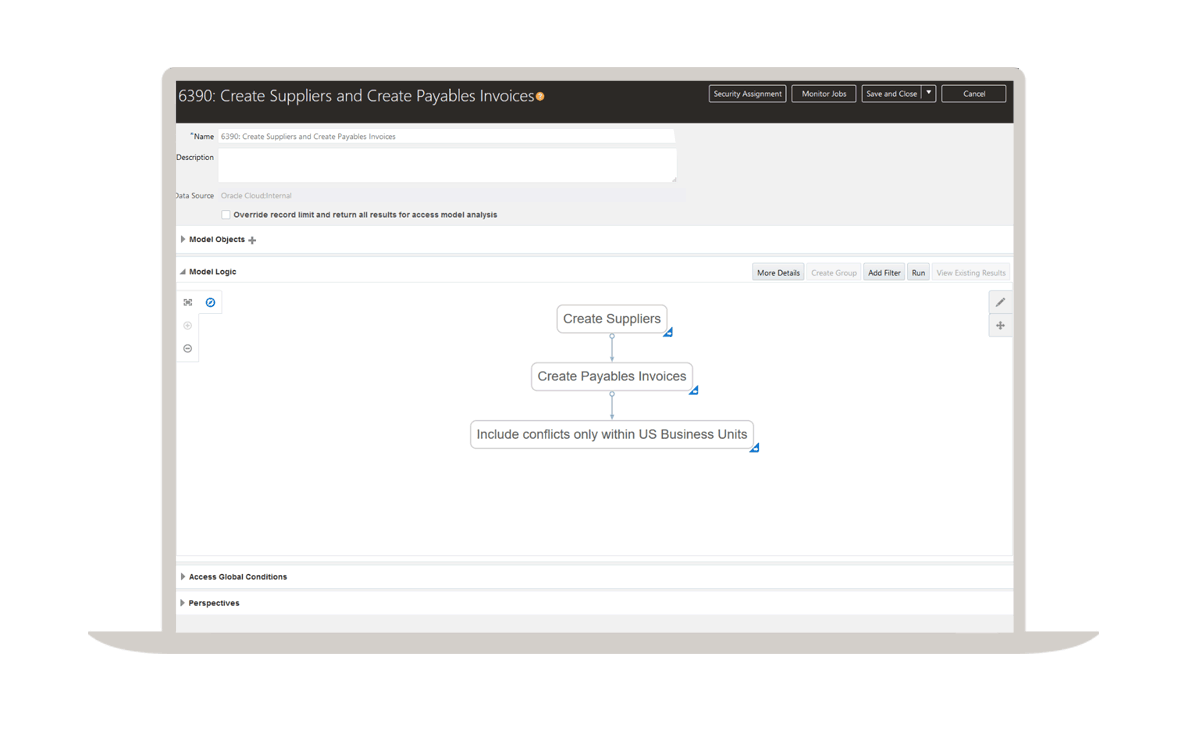
Ensure that access policies, including separation of duties, are enforced in role design as well as user provisioning with preventive and detective methods.
Monitor IT admin/superuser access and transactions
Highly privileged IT users have broad access for activities that require their attention, expertise, and skills. Ensure that such privileges are used as needed, regularly monitored, and not abused.
Monitor business superuser access and transactions
Certain business analyst users have broad, superuser access to facilitate manipulation of configurations, setups, and master data. Because of their deep functional and process knowledge, it makes sense to give these users broad access can be very powerful—provided safeguards are in place to monitor for unusual activity, such as error or misuse.
Monitor nonhuman account access and transactions
In an increasingly automated world, there are many processes that use aliases, APIs, and automated interfaces. Ensure that all nonhuman interfaces are scrutinized, adequately tested, certified, and monitored for changes and updates.
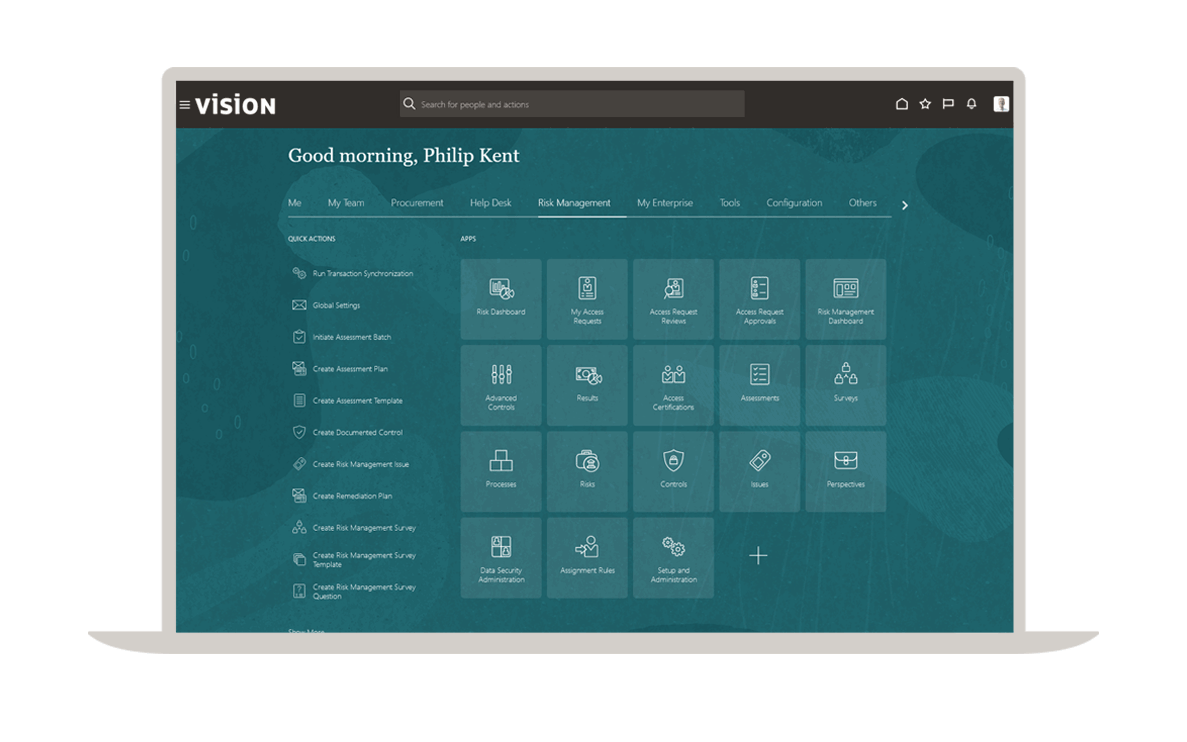
Automate monitoring and control of user access
Design custom roles without separation of duties (SoD) violations
Use a library of prebuilt security rules to ensure your roles are compliant before you go live with your ERP system. Avoid user acceptance testing (UAT) delays, audit findings, and costly remediation of roles.
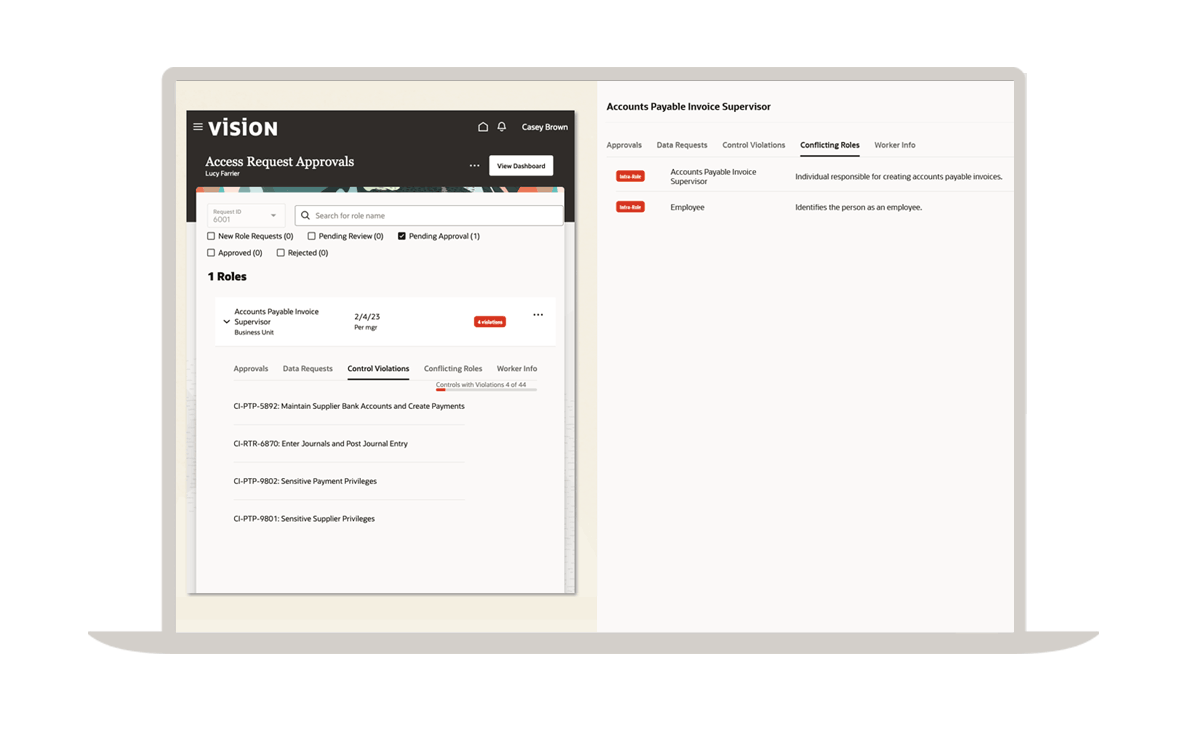
Check access requests for SoD violations
Enable self-service user access requests and help prevent SoD conflicts prior to provisioning access. Route access requests to business process owners for review, document exceptions, and grant access if approved.
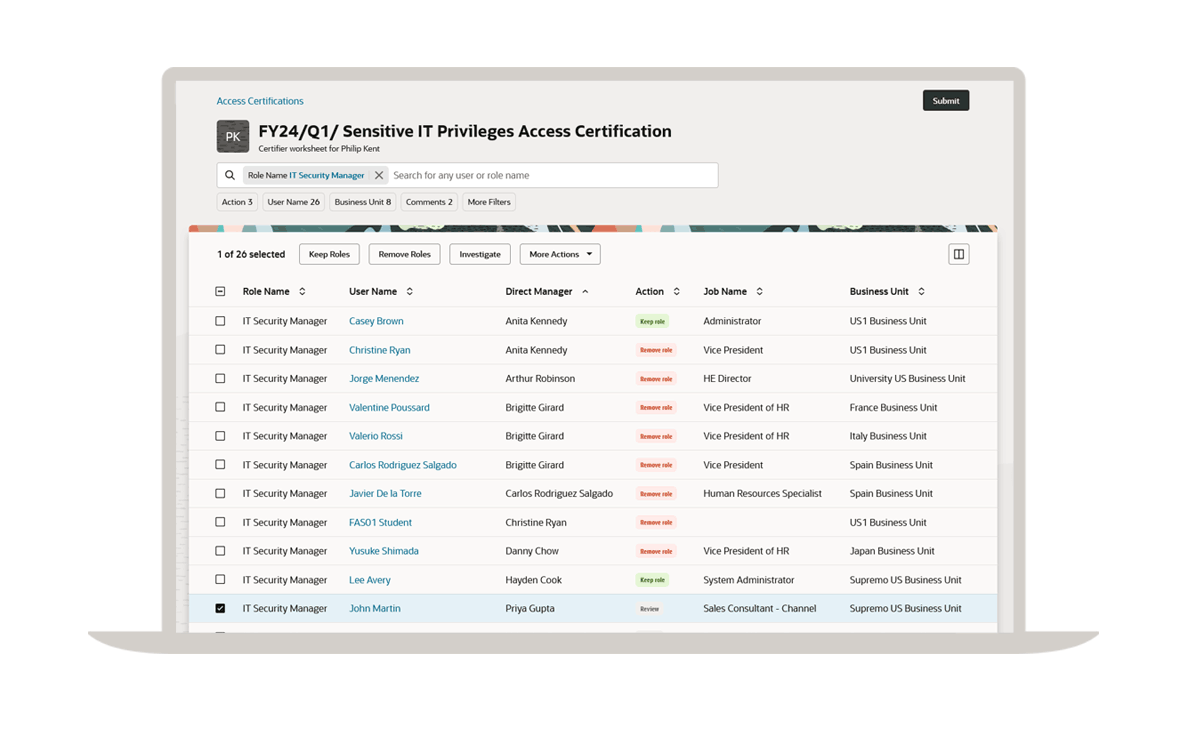
Monitor and report sensitive (restricted) access
Identify users who have been granted sensitive access privileges and data to report, certify, or remove.
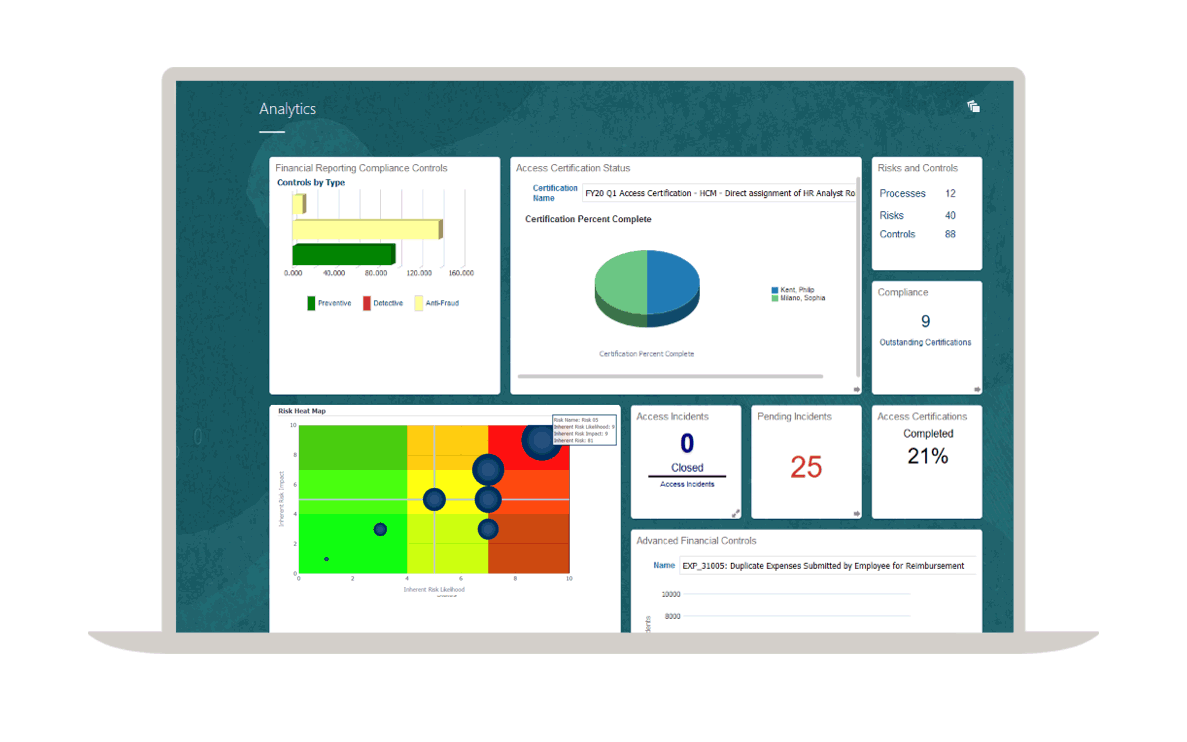
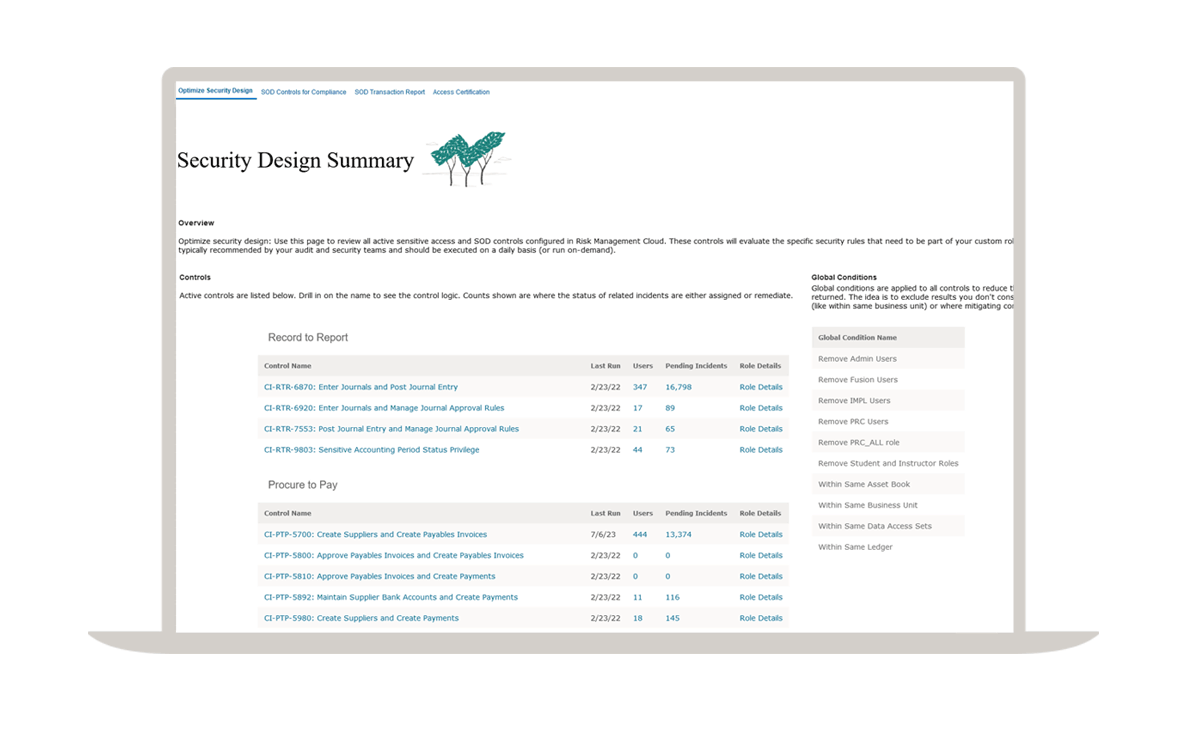
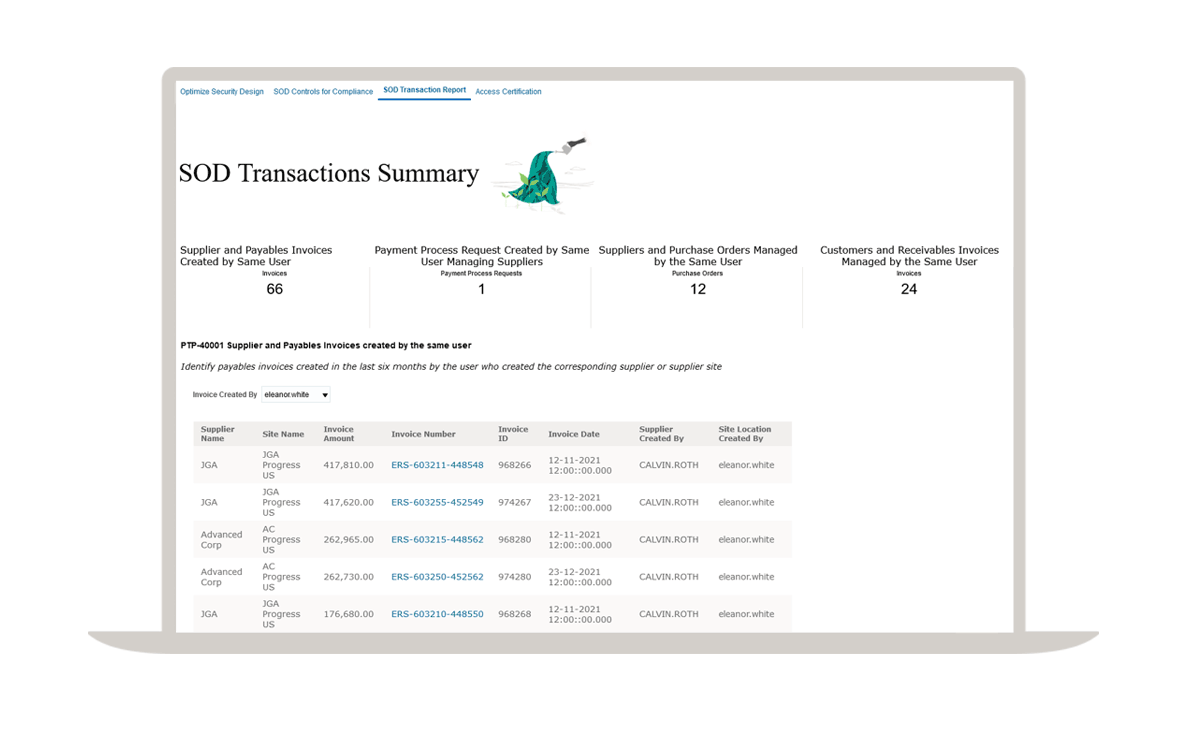
Monitor and report separation of duties
Confidently generate SoD reports to address audit and compliance (ICFR/SOX) requirements.
Automate user access reviews and certifications
Automate user access review workflows to ensure access is authorized by business process owners and meet audit and compliance requirements.
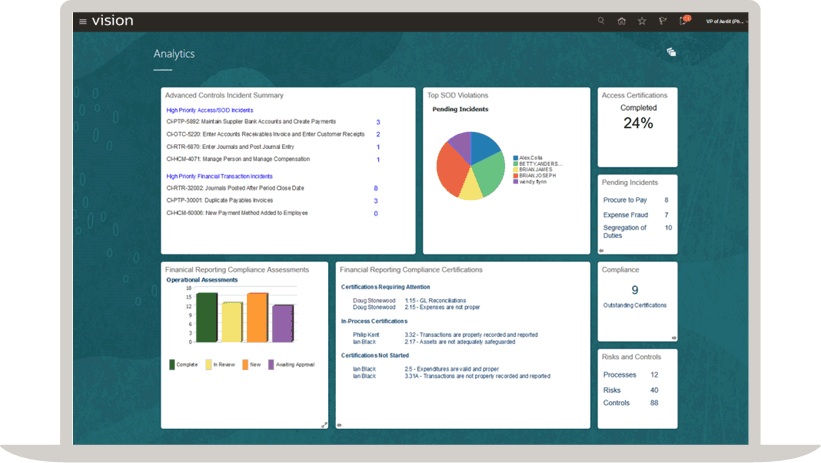
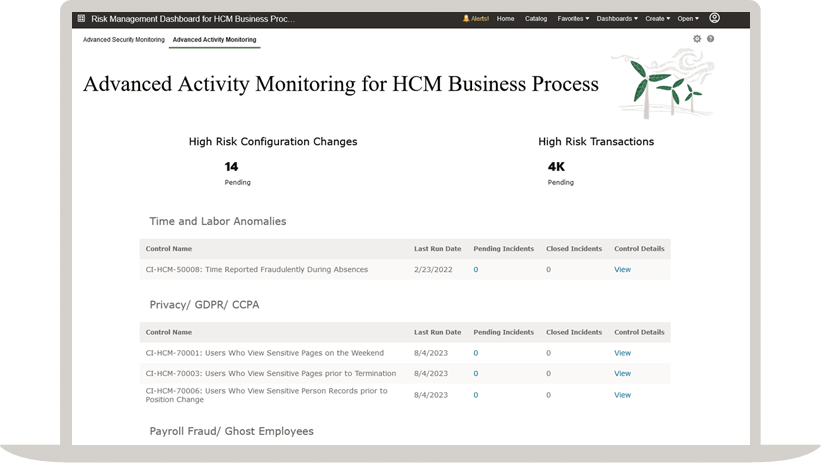
Continuously monitor user activity with AI
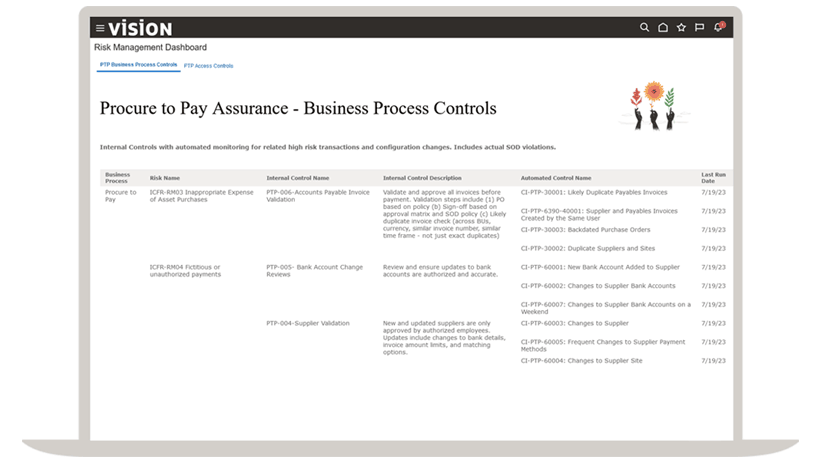
Monitor changes to critical configurations
Automate monitoring of changes to critical configurations to identify unauthorized or suspicious changes.
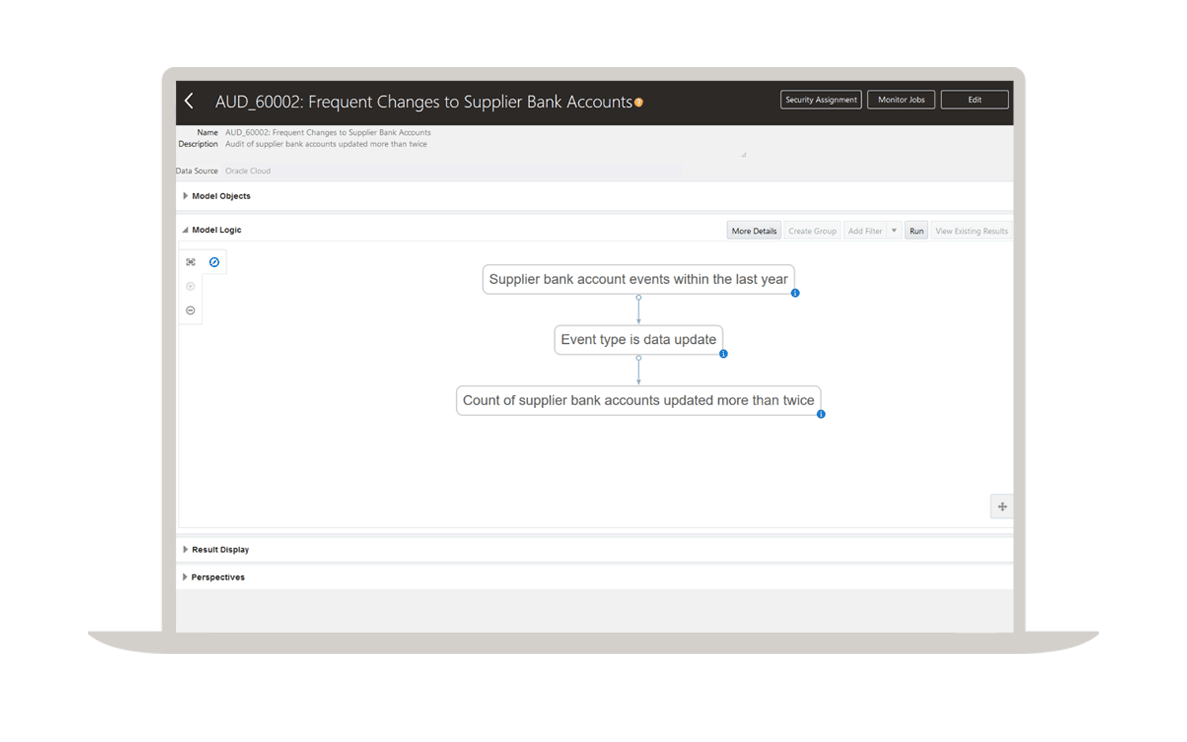
Audit transactions to identify fraud, error, and policy violations
Evolve from sampling to continuous monitoring of financial transactions to ensure complete oversight.
Procure-to-pay assurance
Monitor user access and activity across procure-to-pay to help ensure process integrity. Enforce separation of duties and analyze all purchase orders, invoices, and payments.
Record-to-report assurance
Monitor user access and activity across record-to-report to maintain the integrity of processes. Enforce separation of duties and analyze all subledger transactions, period close adjustments, and manual journal entries.
Order-to-cash assurance
Monitor user access and activity across order-to-cash. Enforce separation of duties and analyze all customer orders, approved credit limits, and payment receipts.
Hire-to-retire assurance
Monitor user access and activity across the hire-to-retire process. Enforce separation of duties and analyze all payroll runs, compensation changes, and time card transactions.
Manage internal controls
Design and document internal controls
Collaborate efficiently and effectively to design, document, and assess internal controls, using a risk-based approach and a unified repository for your internal controls.
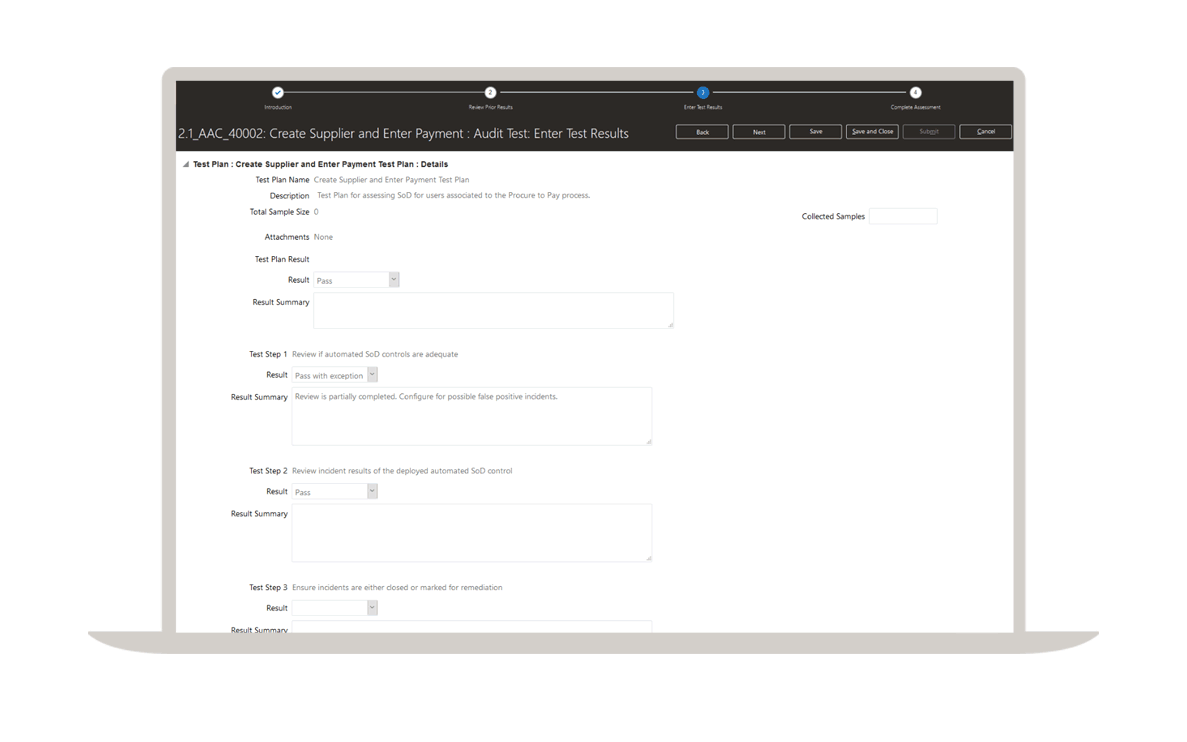
Certify internal controls over financial reporting (ICFR/SOX)
Ensure strong internal controls and audit readiness. Automate periodic testing and certification of controls with intuitive workflows.
Product Tour—Fusion Cloud Risk Management
"We process a huge number of transactions every day, and it would be impractical to review each and every one for error or fraud. Oracle Cloud Risk Management automates this process and helps us create a culture of continuous monitoring with advanced access controls, advanced financial controls, and financial reporting compliance."
—Rich Christensen, SVP and Chief Accounting Officer, TrueBlue
Risk Management and Compliance benefits
Secure ERP access privileges and data
Protect against fraud and error by continiously monitoring transactions and sensitive ERP data with AI technology.
Ensure audit ready processes
Reduce audit expenses by designing secure ERP roles before the system goes live.
Automate risk and compliance activities
Reduce compliance fatigue and save hours of manual effort with easy-to-use workflows and reporting tools.
Build a risk-intelligent culture
Focus on proactive risk management to engage your broader organization in identifying risks and responding with agility.
Resources

Cloud update readiness and product documentation
Want to know what’s new in Oracle Cloud? Check out the Cloud Update Readiness section for updates, documentation, and tutorials.

Collaborate with Oracle and our customers
Join our premier online cloud community to share best practices, chat with product experts, collaborate with your peers, and post ideas for new product features.

Expand your knowledge
Learn how to use Oracle Cloud ERP to manage accounting, projects, procurement and risk.
Learning opportunities

How can we help you?
Related cloud applications
Oracle Bulut ERP'yi kullanmaya başlayın
ERP demosu talep edin
Uzmanlarımızdan biriyle birlikte öğrenin.
ERP ürün turuna katılın
Oracle Bulut ERP'yi kendiniz keşfedin.
SaaS ERP satış ekibiyle iletişim kurun
Ekibimizin bir üyesiyle Oracle Bulut ERP hakkında konuşun.