

Zimperium saves 15% and helps protect the world from mobile threats with OCI
October 11, 2023 | 6 minute read
Authored by Kellsey Ruppel, principal product marketing director at Oracle.

Zimperium empowers enterprises to secure their mobile endpoints, enabling employees to access sensitive data and mission-critical systems safely and securely. The company has developed several mobile threat defense software solutions, and uses machine learning (ML) to offer real-time, on-device protection against Android, iOS, and Chromebook attacks. Zimperium developed its z9 threat detection engine specifically to spot mobile threats, helping protect mobile devices and apps against device, network, phishing, and malicious app attacks.
Goals for cloud migration
With customers across the globe, Zimperium needed an IT architecture that can support its application deployments across multiple regions in a secure, stable, and resilient environment. The team’s technologists also wanted to use containers managed with Kubernetes to build a solution in one region and efficiently extend it around the world. The team also needed to meet various compliance and regulatory requirements, such as the ability to deploy applications in separate networks.
Why Zimperium chose Oracle
Zimperium implemented OCI Kubernetes Engine (OKE) running on Oracle Cloud Infrastructure (OCI), to get a highly scalable and fully managed service to deploy containerized applications. Some of the applications the company offers don’t fit conventional provisioning requirements for cloud-based compute and memory, so the flexible sizes offered by OCI let the company customize provisioning to its applications, resulting in cost savings and efficiency gains.
Oracle’s production support teams also played an important part in Zimperium’s decision to choose Oracle. The ability to work together with support teams when building infrastructure, such as Terraform scripts, made for easier integration with OCI and more successful deployments.
Another feature that was attractive to Zimperium was Oracle’s cost positioning in the global market. With the same pricing plans across all available regions globally, the company could strategically plan in an efficient way, minimizing operational expenses (opex).
“By partnering with Oracle, we have been able to reduce costs, get better performance, and deploy our cloud-based solution in more geographical locations than ever before,” said Shridhar Mittal, CEO of Zimperium.
Suite of Oracle products used
OCI includes all the services needed to migrate, build, and run IT in the cloud, from existing enterprise workloads to new cloud native applications and data platforms. Zimperium used the following OCI services and technologies:
- Region: An OCI region is a localized geographic area that contains one or more data centers, called availability domains. Regions are independent of other regions, and vast distances can separate them, across countries or even continents.
- Availability domain: Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure, such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Virtual cloud network (VCN) and subnets: A VCN is a customizable, software-defined network that you set up in an OCI region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Security list: For each subnet, you can create security rules that specify the source, destination, and type of traffic that must be allowed in and out of the subnet.
- Route table: Virtual route tables contain rules to route traffic from subnets to destinations outside a VCN, typically through gateways.
- Internet gateway: The internet gateway allows traffic between the public subnets in a VCN and the public internet.
- Service gateway: The service gateway provides access from a VCN to other services, such as OCI Object Storage. The traffic from the VCN to the Oracle service travels over the Oracle network fabric and never traverses the internet.
- Load balancer: The OCI Load Balancing service provides automated traffic distribution from a single entry point to multiple servers in the back end.
- File storage: The OCI File Storage service provides a durable, scalable, secure, enterprise-grade network file system. You can connect to a File Storage service file system from any bare metal, virtual machine, or container instance in a VCN. You can also access a file system from outside the VCN by using OCI FastConnect and IPSec VPN.
- OCI Kubernetes Engine (OKE): OKE is a fully managed, scalable, and highly available service that you can use to deploy your containerized applications to the cloud. You specify the compute resources that your applications require, and OKE provisions them on OCI in an existing tenancy. OKE uses Kubernetes to automate the deployment, scaling, and management of containerized applications across clusters of hosts.
- Registry: OCI Registry is an Oracle-managed registry that enables you to simplify your development-to-production workflow. Registry makes it easy for you to store, share, and manage development artifacts, like Docker images. The highly available and scalable architecture of OCI ensures that you can deploy and manage your applications reliably.
- Compute: The OCI Compute service enables you to provision and manage compute hosts in the cloud. You can launch compute instances with shapes that meet your resource requirements for CPU, memory, network bandwidth, and storage. After creating a compute instance, you can access it securely, restart it, attach and detach volumes, and terminate it when you no longer need it.
Migration path
Zimperium deployed its application stack by using OCI Kubernetes Engine (OKE). The application workload is deployed on a private subnet and is isolated from the public internet using a public load balancer for traffic intake. The solution uses NGINX as a private internal load balancer for directing traffic to different application components running on Docker containers.
For its customer data management layer, Zimperium has standardized on the PostgreSQL open source database, which it deploys on a multinode cluster running on OCI Compute instances. These Compute instances are replicated across multiple availability domains and regions worldwide. The PostgreSQL cluster is deployed using Terraform scripts coupled with Ansible and a Python-based approach to make PostgreSQL highly available, including etcd, pgbouncer, haproxy and keepalived for failure detection and VIP failover. Other open source components include Elastic Search and MongoDB in a cluster configuration to support agility, scaling, and business continuity.
The same infrastructure architecture is deployed globally across other OCI regions.
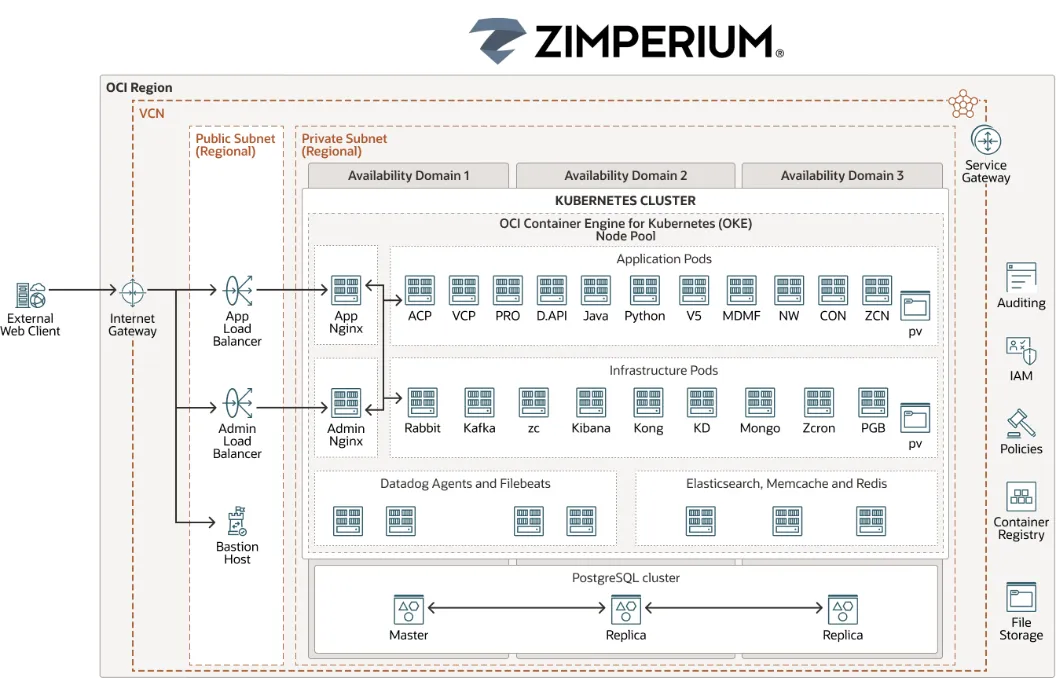
Figure 2: A graphic depicting the reference architecture for Zimperium’s deployment solution.
Results
Zimperium containerized all its components using Docker and used Kubernetes to launch and manage applications. OKE and OCI Functions gave Zimperium a more stable and reliable solution, letting staffers deploy across multiple availability domains, which improved business continuity. The company managed multiregion deployments on OCI without using custom scripts because every Oracle region is identical. For this reason, Zimperium could build a solution in one region and using OCI implement that solution in any Oracle Cloud region with the same level of security and resilience.
Taking advantage of economies of scale, Zimperium’s operations team used a multitenant architecture for customers, resulting in cost savings. However, if a customer requested its data on a single tenancy, the company could offer that option with OCI.
Using a VCN on OCI, Zimperium segregated its architecture into a private and public subnet., which allowed the company to further classify how it exposed its applications and data. It restricted access to authorized individuals using the private subnets for access to logs and administrative tools.
The business incorporated a Datadog element in its architecture and used a cloud application for monitoring infrastructure and applications. OKE provided built-in integration, letting the company continue using Datadog Oracle monitoring services across different regions.
With added features of OCI that came at no extra cost, such as OKE, Zimperium further reduced TCO. Overall, the company saw an approximate savings of 15% after hosting its solution on OCI.
Next steps
For more information on Zimperium and Oracle Cloud Infrastructure, see the following resources:
-
Kellsey Ruppel
Principal Product Marketing Director, Oracle