How an Oracle team spotted ‘StreamScam,’ the biggest connected TV ad scam yet
The team at Oracle Moat, a service for digital advertising companies, detected a rip-off in which bots pretended to be people watching shows via streaming video.
By Mitch Wagner | January 2021

The team at Oracle Moat–including Chris Tsoufakis (left) and Aaron Eppert–exposed a bot scam ripping off Connected TV (CTV) advertisers.
The COVID-19 quarantine has created an explosion in demand for streaming video, whether we’re weeping with the family on This Is Us or solving crimes with NCIS. All that streaming has also created a chance for fraud, in the form of bots pretending to be people streaming shows in order to cash in ad dollars.
But if there’s one thing NCIS’s special agent Leroy Jethro Gibbs has taught us, it’s that those crooks always slip up in some way. Cybercrooks included, it seems—as a team of Oracle researchers learned when finding what they believe is the largest connected TV ad fraud operation ever exposed.
“We look for tells, things the fraudsters forget. When you attempt to cover your tracks, you always forget some small thing,” says Chris Tsoufakis, Oracle Moat vice president of engineering for measurement products.
Since August, the Oracle team was tracking “StreamScam,” a scheme that spoofed more than 28.8 million US valid household IP addresses, including 3,600 apps and 3,400 unique models of connected TV (CTV).
The team that found the scam works on a service called Oracle Moat, which provides measurement and transparency for digital advertising on the web, smartphones, and connected TVs.
“A big part of what we do is, ‘Was this ad seen by a human as opposed to a bot?’” Tsoufakis says. Digital ads can run on many platforms—phones, computers, apps, web browsers, gaming consoles, or a CTV device such as a Roku or Apple TV. Advertisers want their ads to be seen by humans, but sometimes the ad is accessed by a bot. That’s not always for fraudulent reasons—often the bot is an internet crawler deployed by a search engine.
“Ultimately, in the end, you have a human trying to defraud other humans. They’re going to make mistakes.”
As part of its monitoring, Oracle Moat tracks the types of devices the ads are supposedly being displayed on, using automated tools in conjunction with Oracle analyst teams. Oracle Moat started seeing anomalies.
“Ultimately, in the end, you have a human trying to defraud other humans. They’re going to make mistakes,” says Aaron Eppert, Oracle Moat senior director for software development.
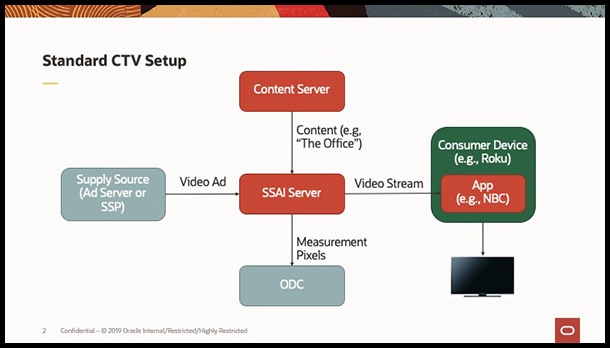
In a standard CTV setup, the SSAI server merges content and ads and delivers the stream to the viewer.
For example, Oracle Moat spotted an unusual number of IP addresses showing six CTV devices per IP, where most households have one or two. The service started seeing an unusual mix of devices, such as Roku, Apple TV, and Google TV devices, disproportionate to real-world consumer usage patterns. Oracle Moat also detected ads supposedly played on Roku devices, yet the claimed device models and software versions were no longer in use among the general population of real Roku users.
After first detecting the botnet in August, the Oracle Moat team rapidly developed signatures to detect the botnet’s presence, similar to the way security researchers develop signatures for particular viruses. Moat deployed those signatures for Oracle Moat customers on September 11. The Oracle Moat team is also sharing information with the Trustworthy Accounting Group (TAG), a global initiative to stop criminal activity and increase trust and transparency in digital advertising.
This isn’t the first big scam Oracle cybersecurity researchers uncovered. In 2019, they uncovered malware dubbed DrainerBot that hijacked Android smartphones to secretly rack up phony video play requests, draining people’s phone batteries and ballooning their data bills in the process.
How StreamScam works
The connected TV scam works by taking advantage of the network architecture used to distribute video ads. Ads are delivered by a server called the supply-side platform, and the programming is delivered by content servers. The server-side ad insertion (SSAI) server merges the two streams and delivers them to the consumer device, to allow seamless transitions between programming and ads.
Within that process, Oracle Moat inserts “measurement pixels” that report on where the ad is served, to verify that the ad was delivered.
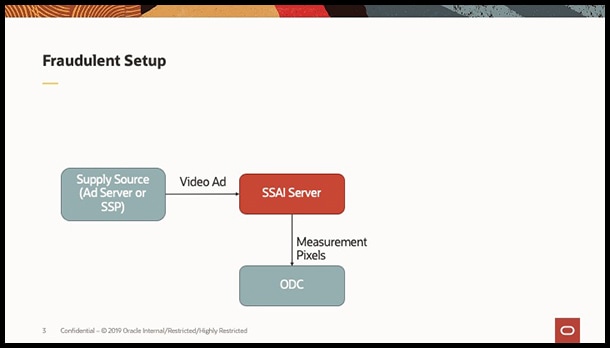
In a fraudulent setup, bots mimic the standard delivery mechanism, and nobody sees the ads.
“Our numbers end up becoming a currency. Advertisers only want to pay for impressions that have been verified by Oracle Moat,” Eppert says.
StreamScam replaces the SSAI server and consumer device with its own software. The bot network sells ad space to middlemen who sell to other middlemen who eventually sell to ad buyers—companies looking to put ads for shampoo or some other product in front of potential customers. Publishers, ad tech platforms, and advertisers use services like Oracle Moat to verify that ads were served to consumers. But StreamScam, it is believed, is defrauding everybody it does business with because bots, not people, are viewing the ads. And bots don’t buy shampoo.
By detecting the fraud, Oracle Moat helps protect ad buyers and everybody in the ecosystem.
Whiteboard beginning
Oracle Moat’s research team began focusing on ad fraud threats in CTV in early 2019, during a meeting in New York City with Oracle teams based there and another that came in from Tel Aviv.
“Nobody knew connected TV was going to explode in 2020,” Eppert says. But the team saw that CTV was becoming a big advertising channel and the next opportunity for fraudsters, and Oracle Moat moved quickly to provide services to this growing market. They developed methods and systems to measure and verify impressions.
Says Eppert: “This happened the way all great things are born in analysis and engineering—it started with a whiteboard.”
Dig deeper
- Oracle exposes largest CTV ad fraud operation ever.
- What happened: A 2020 adtech retrospect.
- Digital ad fraud siphons dollars—and smartphone batteries.
Photography: Oracle

Mitch Wagner
Mitch Wagner is a senior writer at Oracle. He was previously executive editor at Light Reading and at InformationWeek.