Oracle Cloud Native SCCA Landing Zone
The U.S. Department of Defense (DoD) mission is to provide the military forces needed to deter war and ensure our nation's security, and with that comes the challenge of protecting associated information systems. In the last two decades, cloud computing emerged as a technology with tremendous potential, and the DoD has embraced its possibilities. At the same time, cloud computing raises important questions:
- How to reduce operating costs by leveraging cloud economies of scale?
- How to protect DoD’s centralized networks?
- How to protect DoD’s decentralized mission-owner workloads?
- How to share security responsibilities among government and commercial organizations?
- How to leverage unique solutions from each partner without sacrificing interoperability?
- How to enforce security standards in a multi-cloud ecosystem?
In 2018, the DoD released a framework called the Secure Cloud Computing Architecture (SCCA). Building on existing DoD constructs such as NIPRNet (Non-Secure Internet Protocol Router Network) and Information Impact Levels (IL2, IL4, IL5), “the SCCA is designed to meet the boundary protection needs of the Defense Information Systems Network (DISN) by protecting the DISN from cyberattacks originating from within the Cloud Service Provider’s Cloud Service Environment (CSE).” Use the information on this page as guidance—complementing the DoD documents—for achieving SCCA goals.
A brief history—before SCCA
To understand the need for SCCA, it helps to understand what came before SCCA.
Information Impact Levels:
In 2015, the Defense Information Systems Agency (DISA) noted that information comes in different impact levels (IL), and that information systems need to be rated according to the level of information protection they provided. The DoD identified these information impact levels:
- IL 1: Unclassified information approved for public release
- IL 2: Noncontrolled unclassified information
- IL 4: Controlled unclassified information
- IL 5: Controlled unclassified Information–Mission Critical, National Security Systems
As a result, each cloud service provider (CSP) supporting the DoD must go through an accreditation process for each cloud region to determine its IL level. As an example, the following Oracle Cloud regions have IL4/5 accreditation:
Oracle Cloud Region |
Information Impact Level |
Connects to BCAP |
|---|---|---|
| U.S. DoD East | IL4/IL5 | Yes |
| U.S. DoD North | IL4/IL5 | Yes |
| U.S. DoD West | IL4/IL5 | Yes |
| U.S. Gov East | IL4 | No |
| U.S. Gov West | IL4 | No |
Cloud Computing–Security Requirements Guide:
The IL levels listed above were part of a broader document called the “Cloud Computing – Security Requirements Guide” (CC SRG). The Defense Information Systems Agency (DISA) created this document in 2015 to provide detailed requirements on what a commercial cloud region needed to provide adequate protection of DoD information. This document included sections on:
- Information system objectives/impact levels
- Risk assessment of cloud service offerings
- Security requirements
- Cyberspace defense and incident response
- Roles and responsibilities
Networks–NIPRNet, SIPRNet:
In today’s interconnected world, the network itself is both a vital asset and a potential threat vector. The DoD, working alongside the Intelligence Community (IC), uses two networks below that are “fit for purpose” for specific workload categories:
Government Network |
Purpose |
|---|---|
| NIPRNet | Unclassified information |
| SIPRNet | Classified information, up to and including Secret |
Each of these prior security constructs was successful and provided guidance to industry partners on how to offer solutions that meet DoD needs. By 2017, the DoD saw new emerging needs that motivated the creation of an additional framework: SCCA.
SCCA roles and responsibilities
If your organization is considering a SCCA, an important question to ask is, “What role will we play?”
The SCCA FRD identifies three primary SCCA roles:
SCCA Role |
Description |
|---|---|
| Mission owner (MO) | A DoD entity responsible for delivering and operating a DoD mission system. MOs are responsible for the procurement, deployment, and secure operations of mission systems deployed to the cloud environment. Accordingly, MOs are expected to maintain trusted configuration baselines and to perform continuous monitoring for deployed mission systems. |
| Mission cyberspace protection (MCP) | The DoD entity charged with the responsibility of securing a MO’s enclave and networked systems by establishing and delivering cybersecurity capabilities. The MCP is specifically responsible for cyber defense of MO systems. |
| DISN boundary cyberspace protection (BCP) | The DoD entity charged with the responsibility to establish and deliver cybersecurity capabilities to protect the DISN. This entity will be DISA. |
For your organization, questions to ask include:
- Roles: “Which role(s) does my organization want to play?”
- Responsibilities: “What will our responsibilities be?”
- CSP enablement: “How do each CSP’s offerings improve my ability to perform these responsibilities?”
Each of these prior security constructs was successful and provided guidance to industry partners on how to offer solutions that meet DoD needs. By 2017, the DoD saw new emerging needs that motivated the creation of an additional framework: SCCA.
Technical components of SCCA
SCCA includes four primary technical components, described below:
SCCA Component |
Description |
|---|---|
| Cloud access point (CAP) |
Connects the DISN or NIPRNet to a commercial cloud. There are three variants of a CAP:
Major functions:
|
| Virtual data center security stack (VDSS) |
Serves as the virtual security enclave protecting applications and data hosted in commercial environments. Core services:
|
| Virtual data center management Service (VDMS) |
Provides the security systems that manage the security posture of the mission owner enclave. Enable mission owners to:
|
| Trusted cloud credential manager (TCCM) |
Controls and monitors privileged user access for cloud environments. The TCCM owns and maintains the cloud credential management plan (CCMP). In contrast to CAP, VDSS, and VDMS, the TCCM is a person (or role) and associated processes and procedures. Responsibilities:
|
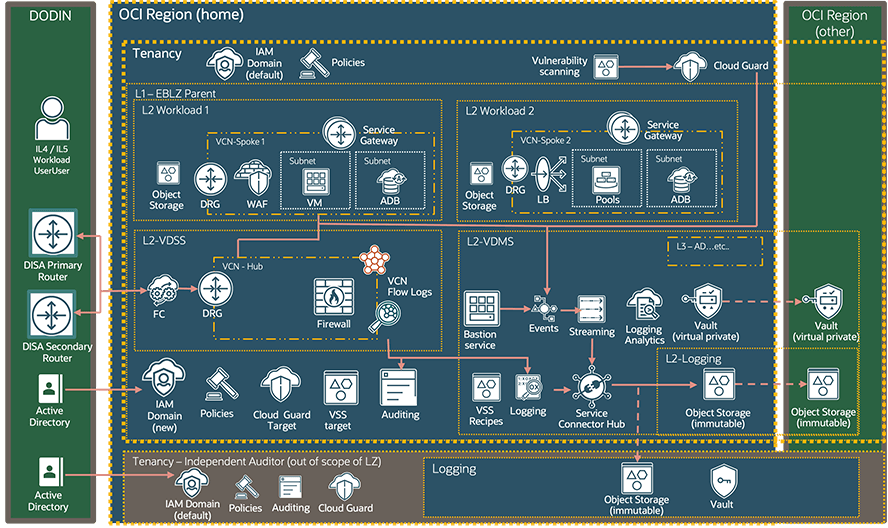
Oracle Cloud Native SCCA Landing Zone Overview
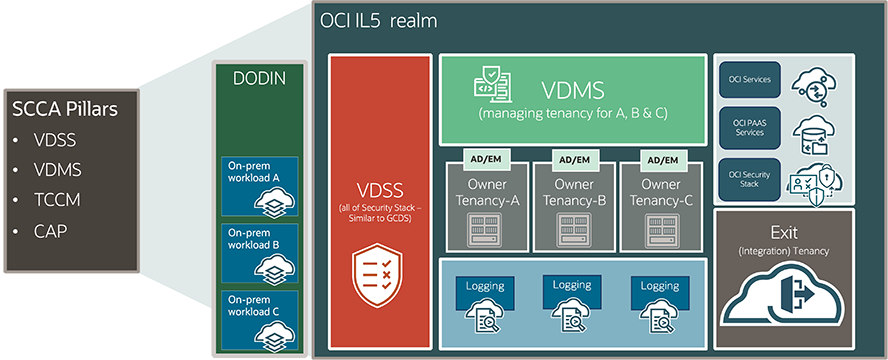
Oracle Cloud Infrastructure (OCI) has introduced a new Secure Cloud Computing Architecture (SCCA) solution for the DoD, making security compliance and cloud adoption for mission-critical workloads easier, faster, and more cost effective by using a framework of cloud native services.
Oracle’s Cloud Native SCCA Landing Zone provides a framework for securely running DoD mission workloads and storing Impact Level 2, 4, and 5 data in OCI government regions. The automation provided by the SCCA Landing Zone enables DoD mission owners to establish a compliant security architecture in just a few hours or days, instead of months. It uses cloud native infrastructure services, significantly accelerating the time to deployment of mission critical workloads by reducing architecture time and minimizing decision points.
Cloud Native SCCA Landing Zones solves mission owner challenges:
Terraform based templates enable you to deploy multiple core services into OCI with the following benefits:
- Onboarding Faster: The templated deployment wizard enables you to move faster by rapidly deploying into OCI rather than wading through documentation yourself.
- Reduce Configuration Drift: Oracle Cloud Native SCCA Landing Zone is repeatable, which means you have consistent deployments each time, reducing and eliminating configuration drift.
- Benefit From Prescriptive Guidance: With all the best practice guidance built into each Landing Zone, you will inherit this best practice through each template and deployment.
Oracle Cloud Native SCCA Landing Zone Architecture
Deployment options for SCCA compliance
Building on DISA’s foundational guidance, the next logical question might be, “How can my organization implement an SCCA-compliant solution using the Oracle Cloud?”
Customers can implement SCCA in four primary ways:
- Implement Oracle Cloud Native SCCA Landing Zone: Oracle’s landing zone wizard includes a pre-ATO’ed configuration to make moving DoD workloads to the cloud simple and efficient.
- Build your own: Oracle has technical briefs and architectural guidance based on what other customers have done. Click below for access to this material.
- Share an existing SCCA environment: Other DoD agencies have already shared their existing SCCA environments in the past, and this can be a quick, low-cost option for you to get started, based on your workload.
- Broker-provided: Some organization serve as an "SCCA Broker", providing an existing solution to DoD agencies for a fee. Cloud One, sponsored by the US Air Force, is one such broker. Following this path can be a very easy and quick way to meet your SCCA compliance requirements.
Contact your Oracle team to discuss these options, and which is best for you.
Additional reference material
- Deploy SCCA-compliant workloads using Oracle Cloud Native SCCA Landing Zone
- Oracle Cloud Security
- Oracle Cloud Infrastructure US Government Cloud with FedRAMP Authorization
- US Government Cloud Customer Documentation
- Oracle Cloud Infrastructure US Federal Cloud with DISA Impact Level 5 Authorization
- 10 Steps to Launch a Secure Cloud Computing Architecture (SCCA) Landing Zone (PDF)